← Exams and Quizzes | Professional Exams →
Notice
If you get a question wrong, you can still click on the other answers. This will open up hints and explanations (if available), which will provide additional information. Exam should be 1 minute per question and please time accordingly.It is not required to have CompTIA A+ certification prior to obtaining CompTIA Network+ certification. It is recommended to have CompTIA A+ certification or the knowledge of the subject matter that is covered under A+ certification exam before taking Network+ certification exam. It is also recommended, but not required, that you have about 12 months of IT networking work experience.
Go to: Set I | Set II
CompTIA Network+ N10-007 - Set III
Congratulations - you have completed CompTIA Network+ N10-007 - Set III.
You scored %%SCORE%% out of %%TOTAL%%. With incorrect multiple attempts, your score is %%PERCENTAGE%%. Your performance has been rated as %%RATING%%
Question 1 |
A | Whaling |
B | Spear phishing |
C | Impersonation |
D | Privilege escalation |
Question 2 |
A | MAC reservations |
B | APIPA |
C | IPv4 to IPv6 tunnel |
D | EUI-64 |
E | IPsec |
Question 3 |
A | LC |
B | ST |
C | MT-RJ |
D | SC |
Question 4 |
A | Honeypots |
B | WPA2 |
C | DMZ |
D | Behavior-based IPS |
E | Signature-based IPS |
Question 5 |
A | Session |
B | Transport |
C | Physical |
D | Network |
E | Data link |
Question 6 |
A | New servers are being provisioned in the cloud |
B | Those servers have host-based firewalls |
C | Some of the servers are configured to use different gateways |
D | Part of the subnet is configured to use different VLANs |
Question 7 |
A | SC |
B | LC |
C | MT-RJ |
D | ST |
Question 8 |
A | Packet sniffer |
B | IDS |
C | Port scan |
D | IPS |
Question 9 |
A | SOP |
B | NDA |
C | SLA |
D | AUP |
Question 10 |
A | CAT3 |
B | CAT6a |
C | Fiber |
D | CAT5e |
Question 11 |
A | Used to determine which port a CAT6 cable is connected. |
B | Used to verify functionality after a NIC is installed. |
C | Used to verify known good patch cables. |
D | Used to terminate a cable at a 110 block. |
E | Used to correct open short on a cable. |
Question 12 |
SSID: SANUJA-WiFi
Signal: 5%
SNR: 2
A | Channel overlap |
B | Incorrect antenna type |
C | Latency |
D | Overcapacity |
Question 13 |
A | FF00::/8 |
B | 2FFE::/16 |
C | FE80::/10 |
D | FEEF:/12 |
Question 14 |
A | Omnidirectional |
B | Unidirectional |
C | Parabolic |
D | Yagi |
Question 15 |
A | Log scanning |
B | Packet capturing |
C | Port scanning |
D | Baseline review |
Question 16 |
A | Public IP |
B | Virtual IP |
C | Reserved IP |
D | Loopback IP |
Question 17 |
A | Out-of-band modem |
B | Out-of-band console router |
C | ACL allowing only Telnet |
D | ACL allowing only HTTP |
Question 18 |
A | Vulnerability report |
B | Rollback plan |
C | Business continuity plan |
D | Baseline report |
Question 19 |
A | MDF |
B | IDF |
C | Switch |
D | CSU/DSU |
Question 20 |
A | Serial |
B | Multimode |
C | Coaxial |
D | UTP |
Question 21 |
A | Full mesh |
B | Partial mesh |
C | Hub and spoke |
D | Bus |
E | Ring |
Question 22 |
A | Physical diagram |
B | Network baseline |
C | Change management log |
D | Logical diagram |
Question 23 |
A | Reflection |
B | Absorption |
C | Channel overlap |
D | Frequency mismatch |
Question 24 |
A | Switch to AP |
B | Router to switch |
C | PC to switch |
D | Router to modem |
E | PC to PC |
Question 25 |
A | WAPs are transmitting on same channel |
B | WAP SSIDs are matching |
C | WPA should be enabled |
D | PKI should be turned off |
Question 26 |
A | CSMA/CA |
B | CSMA/CD |
C | OSPF |
D | MPLS |
Question 27 |
A | Mesh |
B | Ring |
C | Star |
D | Bus |
Question 28 |
A | NAC |
B | ACL |
C | SDN |
D | Traffic shaping |
E | NTP |
Question 29 |
A | RDP |
B | HTTP |
C | NTP |
D | SMTP |
Question 30 |
A | The network administrator should install and configure a DMZ server |
B | The network administrator should install and configure a syslog server |
C | The network administrator should install and configure a traffic analysis server |
D | The network administrator should install and configure a network sniffer |
Question 31 |
A | 162.17.43.22 |
B | 152.119.25.213 |
C | 172.23.226.34 |
D | 132.216.14.184 |
Question 32 |
A | The web server is placed in bridge mode, the router is placed behind the web server, and the modem is placed behind the router |
B | The switch is placed in bridge mode, the modem is placed behind the router, and the router is placed behind the modem |
C | The router is placed in bridge mode, the modem is placed behind the router, and the web server is placed behind the modem |
D | The modem is placed in bridge mode, the router is placed behind the modem, and the web server is placed behind the router |
Question 33 |
A | MIMO |
B | Increase the signal |
C | Disable SSID |
D | Channel bonding |
Question 34 |
A | Bus |
B | WLAN |
C | Ring |
D | Star |
Question 35 |
A | Simple Network Management Protocol (SNMP) |
B | DCCP |
C | SCTP |
D | Packet sniffer |
E | SNMP |
Question 36 |
A | Switching loop |
B | STP blocking |
C | IP addresses |
D | MTU mismatch |
Question 37 |
A | Network log files |
B | Change management records |
C | Logical diagrams |
D | Inventory management |
Question 38 |
A | Modem |
B | Hub |
C | Switch |
D | Router |
Question 39 |
A | BYOD policy |
B | Remote access policy |
C | Incident response policy |
D | DLP policy |
Question 40 |
A | T3 |
B | OC3 |
C | DS3 |
D | E3 |
Question 41 |
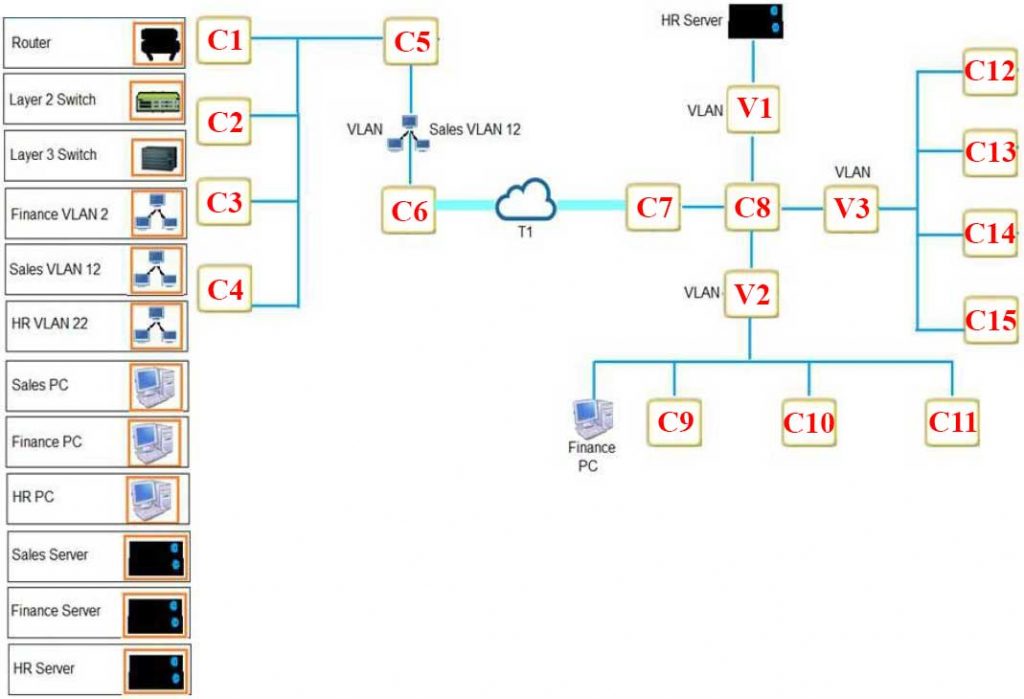
Requirements:
– The remote Sales Team must be able to connect to the corporate network.
– Each department must have ONLY two PCs and a server.
– Eqach department must be segmented from each other.
– The following VLANs have been designed:
— VLAN 2 Finance
— VLAN 12 Sales
— VLAN 22 Human Resources (HR)
– Routing for VLAN 12 is implemented on the router. Routing for VLAN 2 and VLAN 22 is on the switch.
According to the following network diagram for Company A, where would you place the Layer 2 and Layer 3 switches? Click on the image to enlarge.
A | Layer 2 at C7 and Layer 3 at C6 |
B | Layer 2 at C10 and Layer 3 at C12 |
C | Layer 2 at C8 and Layer 3 at C6 |
D | Layer 2 at C6 and Layer 3 at C6 |
E | Layer 2 at C5 and Layer 3 at C6 |
Question 42 |
A | Hub |
B | IDS |
C | Router |
D | IPS |
E | Network tap |
F | Switch |
Question 43 |
A | Enable wireless multimedia (WMM) for QoS |
B | Enable access point antenna isolation |
C | Use the 40MHz channels in the 2.4GHz band |
D | Limit the clients to 802.11g compatible laptops |
Question 44 |
A | Flood guard |
B | BPDU guard |
C | DHCP snooping |
D | Spanning tree |
Question 45 |
A | Signal-to-noise ratio |
B | Packet loss |
C | Attenuation |
D | Reflection |
E | Interference |
F | Latency |
Question 46 |
A | Connect utilizing client-to-site VPN |
B | Allow RDP through an external firewall |
C | Use TFTP to transfer files to corporate resources |
D | Utilize an SSH connection to the corporate server |
Question 47 |
A | ping |
B | nslookup |
C | netstat |
D | pathping |
E | tracert |
F | tcpdump |
G | route |
Question 48 |
A | PPP |
B | MPLS |
C | Frame relay |
D | ATM |
Question 49 |
A | Distance limitations |
B | Latency |
C | Absorption |
D | Security type mismatch |
Question 50 |
A | Switches packets between same subnets based on IP addresses |
B | Switches packets within the same subnet based on MAC addresses |
C | Switches packets between different subnets based on IP addresses |
D | Switches packets between different subnets based on MAC addresses |
Question 51 |
A | Check port 636 to see if it is being blocked |
B | Verify the browser is using port 443 |
C | Restart the web server |
D | Change service port 636 to port 389 |
Question 52 |
A | iSCSI |
B | Fibre Channel |
C | NAS |
D | InfiniBand |
Question 53 |
A | Block traffic from the wireless access point |
B | Packet filtering on the wireless access point |
C | Content filtering on the wireless access point |
D | Allow traffic from the wireless access point |
Question 54 |
A | Multipath support |
B | Channel bonding |
C | Channel expansion |
D | Gigabit wireless bandwidth |
Question 55 |
A | TCP port 25 |
B | UDP port 22 |
C | TCP port 22 |
D | UDP port 53 |
E | UDP port 69 |
Question 56 |
A | The SET function pushes an alert to the MIB database |
B | A response message is sent from the agent to the manager |
C | The object identifier is modified and reported during the next monitoring cycle |
D | A trap message is sent via UDP to the monitoring workstation |
Question 57 |
A | Shared secret |
B | Soft spoken |
C | Private certificate |
D | HTTPS server |
Question 58 |
A | MS-CHAP |
B | CHAP |
C | Kerberos |
D | NTLM |
Question 59 |
A | VoIP endpoint |
B | Router |
C | Access point |
D | Range extender |
Question 60 |
A | Broadcast |
B | Multicast |
C | Unicast |
D | Subnetting |
Question 61 |
A | Buffer overflow attack |
B | Smurf attack |
C | MITM |
D | Social engineering |
E | NMAP |
Question 62 |
A | Reflective |
B | ARP poisoning |
C | DNS poisoning |
D | Evil twin |
E | Ransomware |
F | Man-in-the-middle |
Question 63 |
A | Shared secret keys |
B | MAC filtering |
C | AES encryption |
D | Strong RC4 encryption |
E | Key rotation |
Question 64 |
A | Router ACL |
B | Client-to-site VPN |
C | HTTPS management URL |
D | Out-of-band management |
Question 65 |
A | 128 bits |
B | 256 bits |
C | 32 bits |
D | 64 bits |
Question 66 |
A | Fiber type mismatch |
B | Fiber cable mismatch |
C | Bad fiber switch |
D | Bend radius exceeded |
Question 67 |
Requirements:
– The remote Sales Team must be able to connect to the corporate network.
– Each department must have ONLY two PCs and a server.
– Each department must be segmented from each other.
– The following VLANs have been designed:
— VLAN 2 Finance
— VLAN 12 Sales
— VLAN 22 Human Resources (HR)
– Routing for VLAN 12 is implemented on the router. Routing for VLAN 2 and VLAN 22 is on the switch.
According to the following network diagram for Company A, where should the router be palced? Click on the image to enlarge.
A | C5 |
B | C7 |
C | C10 |
D | C6 |
E | C8 |
Question 68 |
A | FIFO |
B | 802.1x |
C | WPA |
D | MIMO |
E | IPsec |
Question 69 |
A | Point-to-multipoint |
B | Point-to-point |
C | Hybrid |
D | Peer-to-peer |
Question 70 |
A | GBIC |
B | MT-RJ |
C | F-type |
D | BNC |
Question 71 |
A | QoS |
B | SSH |
C | SNMP |
D | L2TP |
Question 72 |
A | Issue a new self-signed certificate. |
B | Upgrade the firmware on the firewall. |
C | Disable the HTTP port in the host firewall. |
D | Generate new SSH host keys. |
E | Remove unnecessary testing accounts. |
Question 73 |
A | 2, 5, 10 |
B | 1, 6, 11 |
C | 3, 13, 23 |
D | 4, 8, 16 |
Question 74 |
A | SNMPv3 |
B | VTP |
C | CDP |
D | IPSec |
Question 75 |
A | Split tunneling |
B | TLS |
C | HTTPS |
D | Remote file access |
Question 76 |
A | Change the channel on the access point to channel 11 |
B | Turn off as many lights in the executive’s office as possible to reduce interference |
C | Turn off SSID broadcasting for the executive’s access point |
D | Replace the 802.11n access point in the office with an 802.11a access point |
Question 77 |
A | Man-in-the-middle |
B | Social engineering |
C | Insider threat |
D | Logic bomb |
Question 78 |
A | Log scanning |
B | Packet capturing |
C | Port scanning |
D | Baseline review |
Question 79 |
A | Syslog |
B | Network map |
C | Placement map |
D | Environmental monitor |
Question 80 |
A | Ticket |
B | Token |
C | Certificate |
D | Time |
Question 81 |
A | Managed switch |
B | Router |
C | Bridge |
D | IDS |
E | Firewall |
Question 82 |
A | Layer 4 |
B | Layer 5 |
C | Layer 1 |
D | Layer 6 |
E | Layer 7 |
F | Layer 3 |
G | Layer 2 |
Question 83 |
A | The channels are overlapping with other wireless networks and should be changed. |
B | The default idle period for logoff is too short and should be changed to a longer limit. |
C | The users have incompatible wireless network cards and should upgrade. |
D | The SSIDs are incompatible and should be renamed. |
Question 84 |
A | Power failure |
B | STP convergence |
C | Excessive bandwidth usage |
D | Broadcast storm |
Question 85 |
A | Plenum Cat 6a |
B | Plenum Cat 5e |
C | PVC Cat 7 |
D | PVC Cat 5 |
Question 86 |
A | MT-RJ |
B | ST |
C | LC |
D | SC |
Question 87 |
A | Phishing |
B | Man-in-the-middle attacks |
C | DoS attacks |
D | Rogue access points |
Question 88 |
A | 00:f3:82:99:a2:b8 |
B | 3ffe:1900:4545:3:200:f8ff:fe21:67cf |
C | 61.23.168.192.in-addr.arpa |
D | 192.168.2.1 |
Question 89 |
A | Replace SFP with a new one |
B | Transpose the fiber pairs |
C | Replace multimode with single-mode cable |
D | Fall back to the old switch |
Question 90 |
A | SaaS |
B | IaaS |
C | CASB |
D | PaaS |
Question 91 |
A | LDAP |
B | NTP |
C | SMTP |
D | IMAP |
E | POP3 |
Question 92 |
IP address: 172.16.204.12
Subnet Mask: 255.255.0.0
Default Gateway: 172.15.204.254
DNS address: 172.16.204.1
Broadcast address: 172.16.255.255
A | Default gateway |
B | DNS address |
C | Broadcast address |
D | Subnet mask |
E | IP address |
Question 93 |
A | White/Orange, Orange, White/Brown, Blue, White/Blue, Green, White/Green, Brown |
B | White/Orange, Orange, White/Green, Blue, White/Blue, Green, White/Brown, Brown |
C | White/Green, Green, White/Blue, Blue, White/Orange, Orange, White/Brown. Brown |
D | White/Green, Green, White/Orange, Blue, White/Blue, Orange, White/Brown. Brown |
E | White/Blue, Orange, White/Green, Blue, White/Orange, Green, White/Brown, Brown |
Question 94 |
A | WEP uses RC4 which is easily accessible and not secure |
B | WEP uses plain text |
C | WEP’s IV is too small |
D | WEP is not well supported |
Question 95 |
A | A network built with Bus Topology |
B | A network built with Mesh Topology |
C | A network built with Star Topology |
D | A network built with Logical Topology |
E | A network built with Ring Topology |
Question 96 |
A | MX |
B | SRV |
C | CNAME |
D | NS |
E | PTR |
Question 97 |
A | AA:CE:58:FD:90:08 |
B | 44:98:3E:F8:33:23 |
C | 56:AD:BX:89:55:54 |
D | 94:9E:FE:EE:8C:DF |
Question 98 |
A | Allow UDP port 3389 outbound |
B | Allow TCP port 3389 outbound |
C | Allow UDP port 3389 inbound |
D | Allow TCP port 3389 inbound |
Question 99 |
A | Incorrect speed/duplex setting on the alarm device |
B | A missing route on the network routers |
C | Incorrect VLAN assignment on the router |
D | A missing route on the alarm device |
Question 100 |
A | MT-RJ |
B | LC |
C | ST |
D | SC |
Question 101 |
A | Rack diagram |
B | IDF/MDF documentation |
C | Logical and physical diagrams |
D | Network performance baseline |
Question 102 |
A | Fingerprint + retina scan |
B | Username + password |
C | Smart card + PIN |
D | Key fob + ID card |
Question 103 |
A | Ping |
B | Protocol analyzer |
C | Nessus |
D | Baseline analyzer |
Question 104 |
A | Channel overlapping |
B | Overcapacity |
C | Interference |
D | DHCP exhaustion |
Question 105 |
- AP encryption forced to WPA2-AES mode only
- MAC address filtering enabled with the following MAC address in the allow list: 00-ab-29-da-c3-40
Which is true about the above configuration?
A | An 802.11a compatible client can connect to the wireless network only if its MAC address is 00- ab-29-da-c3-40 and the encryption key is known by the client. |
B | Any 802.11b/g compatible client can connect to the wireless network if they support TKIP, the MAC address is 00-ab-29-da-c3-40, and the encryption key is known by the client. |
C | Any 802.11g compatible client can connect to the wireless network if the encryption key is known by the client. |
D | An 802.11n compatible client can connect to the wireless network only if its MAC address is 00- ab-29-da-c3-40 and the encryption key is known by the client. |
Question 106 |
A | WAF |
B | WPA |
C | TPM |
D | IDS |
E | DLP |
Question 107 |
Department-VLAN#-Subnet used
Marketing-20-192.168.20.0/28
Customer Service-25-192.168.20.64/28
Finance-30-192.168.30.0/28
WHSE-35-192.168.30.16/28
Sales-40-192.168.3.16/28
The users experiencing this issue need to be added to which of the following VLANs?
A | 35 |
B | 30 |
C | 25 |
D | 40 |
Question 108 |
A | Firewall |
B | Router |
C | Multiplayer switch |
D | Bridge |
Question 109 |
A | Absorption |
B | Attenuation |
C | Refraction |
D | Distance |
E | Reflection |
Question 110 |
| Cable | Test | Result |
|---|---|---|
| 1.2 | Open | 7ft |
| 3.6 | Short | 7ft |
| 4.5 | Open | 7ft |
| 7.8 | Open | 7ft |
A | Toner Probe |
B | OTDR |
C | Punch Down Tool |
D | Protocol Analyzer |
E | Cable Certifier |
F | Multimeter |
G | Crimper |
Question 111 |
A | Install antivirus software and set an ACL on the servers |
B | Install a BPDU guard on switchports and enable STP |
C | Create a VLAN for the unused ports and create a honeyspot on the VLAN |
D | Create a DMZ for public servers and secure a segment for the internal network |
Question 112 |
A | ARP protection |
B | BPDU guard |
C | Spanning tree |
D | DHCP snooping |
Question 113 |
A | Connection speeds decrease |
B | Attenuation increases |
C | Throughput decreases |
D | Cell size increases |
Question 114 |
A | Warm site |
B | Differential backup |
C | Full backup |
D | Cold site |
E | Hot site |
F | Incremental backup |
Question 115 |
A | EIGRP |
B | BGP |
C | OSPF |
D | RIP |
Question 116 |
A | Smart card reader |
B | Asset tracking tags |
C | Biometric locks |
D | Motion detection |
Question 117 |
A | The technician should set up individual routes between the machines. |
B | The technician should connect the machine to its own separate switch. |
C | The technician should configure a virtual switch. |
D | The technician should add a route in each virtual machine to the default gateway. |
Question 118 |
A | pathping |
B | nslookup |
C | route |
D | nmap |
Question 119 |
A | Add a firewall and implement proper ACL. |
B | Add a bridge between two switches. |
C | Add a router and enable OSPF. |
D | Add a layer 3 switch and create a VLAN. |
Question 120 |
A | Forwarding |
B | Blocking |
C | Learning |
D | Disabled |
Question 121 |
A | Punch down tool |
B | Cable tester |
C | Environmental monitor |
D | OTDR |
Question 122 |
A | Distance vector |
B | Static |
C | Link state |
D | Hybrid |
Question 123 |
A | Datagram Transport Layer Security (DTLS) |
B | TFTP |
C | DTLS |
D | SNMP |
E | DNS |
Question 124 |
A | 10.10.50.0/30 |
B | 192.170.10.0/24 |
C | 192.1.0.124/30 |
D | 192.168.0.192/24 |
E | 172.16.20.0/30 |
Question 125 |
A | Wireless firewall |
B | Wireless hub |
C | Wireless bridge |
D | Wireless access point |
Question 126 |
A | EIGRP |
B | IPv6 |
C | ICMP |
D | UDP |
Question 127 |
A | EIGRP |
B | OSPF |
C | RIP |
D | BGP |
Question 128 |
A | 802.11g |
B | 802.11b |
C | 802.11n |
D | 802.11ac |
E | Z-Wave |
Question 129 |
A | CHAP |
B | Digital signatures |
C | MAC filtering |
D | MS-CHAP |
Question 130 |
A | Commonly used on IaaS |
B | Commonly used on SAN |
C | MTU size greater than 10000 |
D | MTU size greater than 1500 |
E | MTU size greater than 12000 |
Question 131 |
A | The WAP transmitter light is dim |
B | The LWAPP image is installed on the WAP |
C | The terminal emulation software is misconfigured |
D | The WAP antenna is damaged |
Question 132 |
A | Increases port speed |
B | Allows another connection to the router |
C | Segments broadcast traffic |
D | Decreases bandwidth on a network |
Question 133 |
A | lsenv |
B | lsshell |
C | getargs |
D | env |
E | ls |
Question 134 |
A | FTP |
B | PPTP |
C | CARP |
D | L2TP |
E | ISAKMP |
Question 135 |
A | Install a UPS |
B | Install a power conditioner |
C | Install a new switch |
D | Replace the switch uplink cable |
E | Install a new electrical circuit |
← |
List |
→ |
| 1 | 2 | 3 | 4 | 5 |
| 6 | 7 | 8 | 9 | 10 |
| 11 | 12 | 13 | 14 | 15 |
| 16 | 17 | 18 | 19 | 20 |
| 21 | 22 | 23 | 24 | 25 |
| 26 | 27 | 28 | 29 | 30 |
| 31 | 32 | 33 | 34 | 35 |
| 36 | 37 | 38 | 39 | 40 |
| 41 | 42 | 43 | 44 | 45 |
| 46 | 47 | 48 | 49 | 50 |
| 51 | 52 | 53 | 54 | 55 |
| 56 | 57 | 58 | 59 | 60 |
| 61 | 62 | 63 | 64 | 65 |
| 66 | 67 | 68 | 69 | 70 |
| 71 | 72 | 73 | 74 | 75 |
| 76 | 77 | 78 | 79 | 80 |
| 81 | 82 | 83 | 84 | 85 |
| 86 | 87 | 88 | 89 | 90 |
| 91 | 92 | 93 | 94 | 95 |
| 96 | 97 | 98 | 99 | 100 |
| 101 | 102 | 103 | 104 | 105 |
| 106 | 107 | 108 | 109 | 110 |
| 111 | 112 | 113 | 114 | 115 |
| 116 | 117 | 118 | 119 | 120 |
| 121 | 122 | 123 | 124 | 125 |
| 126 | 127 | 128 | 129 | 130 |
| 131 | 132 | 133 | 134 | 135 |
| End |
Based on general knowledge and CompTIA guidelines published in 2020.
FAQ | Report an Error
Study outline at: CompTIA Exams Guide
Disclaimer: While every reasonable effort is made to ensure that the information provided is accurate, no guarantees for the currency or accuracy of information are made. It takes several proof readings and rewrites to bring the quiz to an exceptional level. If you find an error, please contact me as soon as possible. Please indicate the question ID-Number or description because server may randomize the questions and answers.