← Exams and Quizzes | Professional Exams →
Notice
If you get a question wrong, you can still click on the other answers. This will open up hints and explanations (if available), which will provide additional information. Exam should be 1 minute per question and please time accordingly.The two cores of A+ exams are very smiliar and the knowlagebase is linked across both exams. I highly recommend that you go through the questions for both core 1 and core 2 compeltely at least once before talking either exam. Then you can you back and study the questions intricately for one of the two cores before taking that specific section exam.
Go to: 220-1001 – Core 1
CompTIA 220-1002 - Core 2
Congratulations - you have completed CompTIA 220-1002 - Core 2.
You scored %%SCORE%% out of %%TOTAL%%. With incorrect multiple attempts, your score is %%PERCENTAGE%%. Your performance has been rated as %%RATING%%
Question 1 |
A | Upgrade the video drivers. |
B | Check the RAM configuration. |
C | Reinstall the Windows OS. |
D | Replace the hard drive. |
E | Reinstall the CAD program. |
Question 2 |
A | User Accounts |
B | Sync Center |
C | Folder Options |
D | Display Settings |
Question 3 |
A | Ls |
B | dirc |
C | Chown |
D | Chmod |
E | Passwd |
Question 4 |

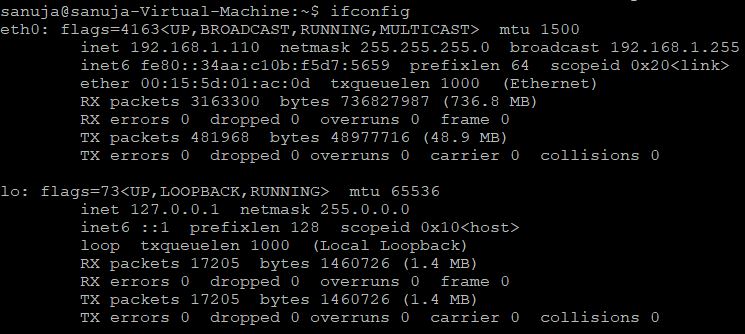
A | This PC Is connected to the LAN via both wired and wireless LAN interfaces. |
B | This PC must be running Windows 7 because only Windows 7 utilities can generate this snapshot. |
C | This PC is connected to a domain called SANUJA and NetBIOS device name is ASUS. |
D | This PC has two LAN interface cards; wired and wireless. But only the wired LAN is connected to a network. |
E | This PC is running low on memory resources with a very high percentage is committed. |
Question 5 |
A | Reboot the router. |
B | Revert the computer back to the last stable Windows service pack. |
C | Reboot the network cameras. |
D | Uninstall firewall applications and disable all firewall rules. |
E | Add the necessary port numbers to the exceptions list of Windows Defender firewall. |
Question 6 |
A | OU Group Policy |
B | Local Security Policy |
C | Site Policy |
D | Active Directory Policy |
Question 7 |
A | Boot into the Safe Mode. |
B | Run Msconfig. |
C | Remove the network card. |
D | Check the System log. |
E | Run Chkdsk. |
Question 8 |
A | ext4 |
B | NTFS |
C | exFAT |
D | FAT32 |
Question 9 |
A | 6 GB |
B | 4 GB |
C | 2 GB |
D | 512 MB |
E | 1 GB |
Question 10 |
A | macOS |
B | Chrome OS |
C | Windows 10 |
D | Android OS |
E | Ubuntu OS |
Question 11 |
A | Escalate to stakeholders and obtain override approval for out-of-scope changes. |
B | Submit the changes to the change board for approval. |
C | Document the changes and perform the work. |
D | Notify the change team of the changes needed and perform the changes. |
E | Obtain end-user acceptance for the proposed changes and submit a change plan for additional work. |
Question 12 |
A | C:\Documents and Settings\%username%\Documents |
B | C:\Users\System32\Documents |
C | C:\Users\%username%\Documents |
D | C:\Users\%root%\Documents |
Question 13 |

A | Windows Control Panel |
B | Windows Task Manager |
C | Performance Monitor |
D | Windows Registry |
E | Windows Task Scheduler |
Question 14 |
A | Rooting |
B | Open shell access |
C | Jailbreaking |
D | VirusBarrier |
E | Grant superadmin |
Question 15 |
A | Seat license |
B | Commercial license |
C | Open source license |
D | Enterprise license |
Question 16 |
A | Gparted |
B | Disk Management |
C | DiskPart |
D | System Management |
E | Event Viewer |
Question 17 |
A | Files |
B | Snap-ins |
C | Applets |
D | Directories |
Question 18 |
A | ipconfig /renew |
B | ping |
C | ipconfig |
D | netstat |
E | ipconfig /all |
Question 19 |
A | dir /? |
B | dir /o |
C | dir /d |
D | dir -1 |
E | dir /a |
Question 20 |
A | msconfig |
B | perfmon |
C | regd |
D | dxdiag |
E | taskmgr |
Question 21 |
A | Safe Mode |
B | ifconfig |
C | Msconfig |
D | Task Manager |
Question 22 |
A | BitDefender |
B | Windows user account |
C | Windows administrator user account |
D | BIOS password |
E | BitLocker |
Question 23 |
A | Dynamic partition |
B | Primary partition |
C | Extended partition |
D | Secondary partition |
E | USB drive |
Question 24 |
A | Windows 10 Pro |
B | Windows 10 Education |
C | Windows 10 Home |
D | Windows 10 Enterprise |
Question 25 |
A | Program Files |
B | Systemroot |
C | System32 |
D | Program Files (x86) |
Question 26 |
A | Unsigned drivers or untrusted software. |
B | VPN configuration or inactive VPN. |
C | Mobile Device Management (MDM) policies |
D | Anti-virous and anti-malware software intefrence. |
Question 27 |
A | Device Manager |
B | Power plans |
C | TRIM |
D | Display properties |
E | Task Manager |
Question 28 |
A | REM |
B | Rebuild |
C | Convert |
D | Replace |
E | Recover |
Question 29 |
A | App Store |
B | Spotlight |
C | Google Play |
D | iTunes |
E | Trusted Mobile Platform (TMP) |
Question 30 |
A | Unicode |
B | ASCII |
C | PS1 |
D | ITU-T |
E | EBCDIC |
Question 31 |
A | .bat |
B | .vbs |
C | .js |
D | .sh |
Question 32 |
A | Grant superadmin |
B | Jailbreaking |
C | Open shell access |
D | VirusBarrier |
E | Rooting |
Question 33 |
A | Component Services |
B | Security Policy |
C | Local Users and Groups |
D | System Configuration |
Question 34 |
A | Microsoft OneDrive |
B | iCloud |
C | Local NAS |
D | Google Cloud Platform |
Question 35 |
A | chain of custody |
B | official documentation |
C | Incident Response Life Cycle |
D | incident response |
E | MSDS |
Question 36 |
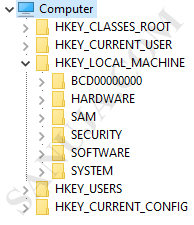
A | HKEY_LOCAL_MACHINE |
B | HKEY_USERS |
C | HKEY_CURRENT_CONFIG |
D | HKEY_CLASSES_ROOT |
Question 37 |
A | Enterprise license |
B | Open license |
C | Personal license |
D | Corporate license |
E | Volume license |
Question 38 |
A | pad and chmod |
B | cp and rm |
C | sudo and vi |
D | ls and chown |
E | ps and kill |
Question 39 |
A | conditional statement , run |
B | loop , iteration |
C | loop , run |
D | conditional statement , iteration |
Question 40 |
A | Windows Registry |
B | Windows Task Manager |
C | Windows Control Panel |
D | MS-DOS Control Panel |
E | Windows Task Scheduler |
Question 41 |
A | This account is designed to provide basic permissions for completing common daily tasks. Users of this account are restricted from performing things like installing new software. |
B | This account is designed for users who require specific administrator rights or permissions. Users of this account are restricted from installing software but can change time zones. |
C | This account is designed for users who require temporary access to a computer and do not need to store user-specific settings. Users of this account have very limited permissions. |
D | This account is designed to have the ability to set permissions for other users on the system. Users of this account have the capability to perform any operation or task on the system. |
Question 42 |
A | GPT |
B | FAT32 |
C | Dynamic drive |
D | MBR |
Question 43 |
A | Lower power consumption. |
B | Support for single large files over 4GB. |
C | Compatibility across different OS providers such as Windows, Linux and Mac. |
D | Better driver encryption and support for cryptology. |
E | Low drive failure rates. |
Question 44 |
A | \%systemroot%\Windows |
B | \%systemroot%\System32\Config |
C | \%systemroot%\System32 |
D | \%systemroot%\Windows\System32\Con
fig |
Question 45 |
A | Disconnect the computer from the office network. |
B | Research the virus and how to remove it. |
C | Rollback OS and driver updates. |
D | Run a System Restore. |
E | Reboot the computer in order to make sure all other programs are terminated. |
Question 46 |
A | chkdsk C: /I |
B | chkdsk C: /C |
C | chkdsk C: /R |
D | chkdsk C: /F |
E | chkdsk /sec |
Question 47 |
A | Adding ports |
B | Enabling sharing |
C | Modifying spool settings |
D | Pausing printing |
Question 48 |
A | Within the Start menu |
B | In the System Properties dialog box |
C | In the System32 folder |
D | On the taskbar |
Question 49 |
A | Secure Shell |
B | SSO |
C | Propagation |
D | MFA |
E | Inheritance |
Question 50 |
A | setupact.log |
B | setuperr.log |
C | unattend.xml |
D | diskmgmt.msc |
Question 51 |
A | /S |
B | /E |
C | /sub-1 |
D | /B |
E | /D |
F | /DCOPY:T |
Question 52 |
A | Multi-boot |
B | Dynamic |
C | PXE |
D | GPT |
Question 53 |
A | Force quit |
B | Control Panel |
C | Task Manager |
D | Computer Management |
E | Tasklist |
Question 54 |
A | Seat license |
B | Commercial license |
C | Open source license |
D | Enterprise license |
Question 55 |
A | diskmgmt.msc |
B | unattend.xml |
C | setuperr.log |
D | setupact.log |
Question 56 |
A | Sigverif |
B | Msconfig |
C | Dxdiag |
D | Ping |
E | Regedit |
Question 57 |
A | Destroy the old hard drive by physically mutilation and cutting the platters into small pieces. |
B | Open the old hard drive case and use ESD to destory the circuitry. |
C | Format the old hard drive multiple times before deposal. |
D | Completely erase the old drive prior to disposal. |
Question 58 |
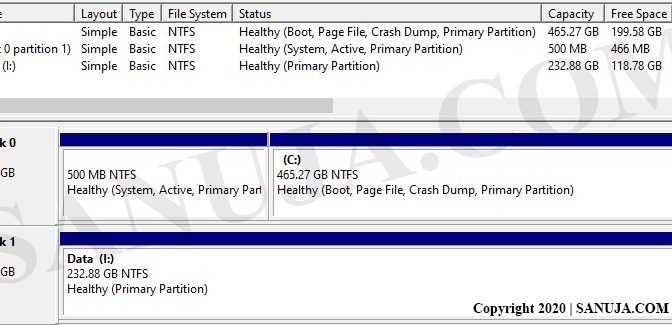
A | Disk 0 |
B | Primary partition |
C | FAT32 partition |
D | Healthy partition |
E | Disk 1 |
Question 59 |
A | Change the user account permissions to restrict access. |
B | Replace the hard drive. |
C | Educate the customer on how to avoid malware. |
D | Do nothing. |
E | Reinstall the antivirous and malware software. |
Question 60 |
A | Disable network cards |
B | Disable all non-administrator accounts. |
C | Disable System Restore |
D | Run the CHKDSK /R command |
E | Run Windows Update |
Question 61 |
A | Impersonation |
B | Spoofing |
C | Spear phishing |
D | Whaling |
Question 62 |
A | Windows+pause break |
B | Windows+M |
C | Ctrl+Alt+Del |
D | Windows+R |
E | Windows+L |
Question 63 |
A | Drive wipe |
B | Standard format |
C | Degauss |
D | Low-level format |
Question 64 |
A | CompTIA |
B | Microsoft |
C | WWF |
D | Apple |
E | IBM |
Question 65 |
A | Center |
B | First left |
C | First right |
D | None of the answers are correct |
Question 66 |
A | Format and partition the drive. |
B | Unplug the power and re-plug it without powering down the workstation. |
C | Run Windows updates. |
D | Visit the website of the SSD manufacturer for firmware updates or contact the manufacturer. |
E | Initialize the drive. |
Question 67 |
A | Windows 10 only comes in 64-bit version. |
B | The 32-bit architecture has an upper RAM limit of 64 GB. |
C | The 64-bit architecture has an upper RAM limit of 128 GB. |
D | The 64-bit version is also known as x86. |
E | The 32-bit CPUs can only address a maximum of 4 GB of RAM, but 64-bit CPUs can address many TBs of RAM. |
Question 68 |
A | Convert the file system to NTFS. |
B | Change the location of the system32 |
C | Disable UAC. |
D | Defrag the hard drive. |
E | Enable TPM in the BIOS/UEFI. |
Question 69 |
The Windows Boot Configuration Data File Is Missing Required Information.
A | boot\bcd |
B | bootrec /fixmbr |
C | bootrec /fixboot |
D | bootrec /restore |
E | bootrec /rebuildbcd |
Question 70 |
A | perfmon.msc |
B | Ipconfig |
C | DxDiag |
D | Regedit |
E | gettingstarted |
Question 71 |
A | Reprimand the user and apply a content filter
to the user’s profile. |
B | Delete the bit torrent application and contact the affected copyright holders. |
C | Secure the workstation in a limited access
facility. |
D | Document the incident and purge all policy-violating materials. |
E | Immediately delete all unauthorized materials. |
Question 72 |
A | VB Script |
B | Command Prompt |
C | PowerShell |
D | DOS |
Question 73 |
A | Run chkdsk. |
B | Partition the drive. |
C | Copy system files. |
D | Defragment the drive. |
Question 74 |
A | Google Android version may be the same but the core APKs are different from manufacture to manufacture. |
B | One of the users most likely is not on Android 10 even though he/she thinks they are on Android 10. |
C | Each manufacturer has their own custom apps which change the behaviour of the GUI. |
D | Each manufacturer has their own customized Launchers that modify the GUI. |
E | The Android Kernel version must be different bvetwen the manufactures. |
Question 75 |
A | wintask |
B | devmgmt.msc |
C | eventvwr.msc |
D | systempropertiesadvanced.exe |
E | perfmon.exe |
Question 76 |
A | .py1 |
B | .ps |
C | .py |
D | .ps1 |
E | .vbs |
Question 77 |
A | .apk |
B | .sdk |
C | .ipa |
D | api |
E | .exe |
Question 78 |
A | Add the user to the local administrators group |
B | Check for and apply software updates |
C | Rebuild the users mail profile |
D | Perform repair installation on the application |
Question 79 |
A | Administrator |
B | Standard user |
C | Guest |
D | Power users |
Question 80 |
A | /B |
B | /S |
C | /sub-1 |
D | /D |
E | /DCOPY:T |
F | /RCOPY |
Question 81 |
A | NTFS supports larger volumes. |
B | NTFS supports file encryption. |
C | NTFS supports larger file sizes. |
D | NTFS supports more file formats. |
Question 82 |
A | Component Services |
B | Device Manager |
C | Performance Monitor |
D | Local Security Policy |
Question 83 |
A | winreg |
B | hives |
C | reg |
D | registry |
E | regedit |
Question 84 |
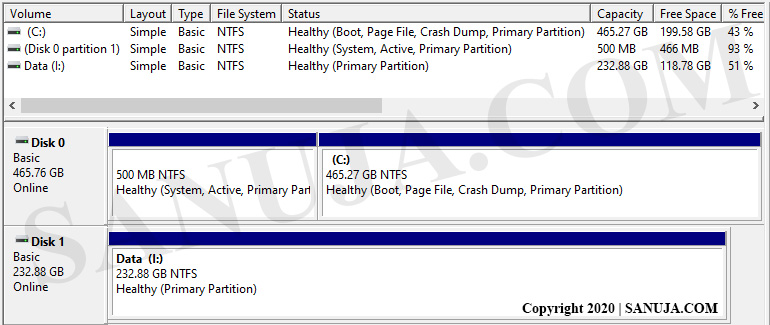
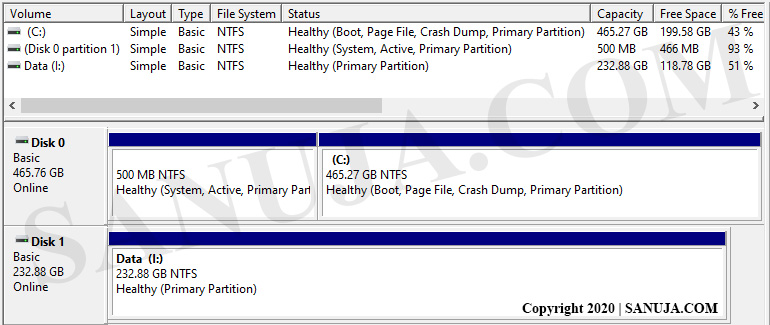
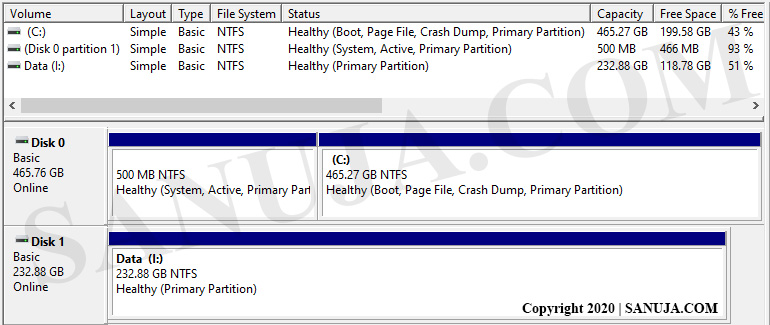
A | Disk 1 |
B | None of the partitions can be dismounted without crashing the system. |
C | Disk 0 - 500 MB NTFS |
D | Disk 0 - 465.27 MB NTFS |
Question 85 |
A | Memory |
B | Hard drive/SSD |
C | CD-ROM |
D | Driver |
Question 86 |
A | Windows Aero |
B | Windows Domain |
C | HomeGroup |
D | Sync Center |
E | Windows Defender |
Question 87 |
A | Install to a network drive |
B | Install to a secondary internal HDD |
C | Install to a USB drive |
D | Install to a DVD-RW |
Question 88 |
A | chkdsk C: /I |
B | chkdsk C: /C |
C | chkdsk C: /R |
D | chkdsk /sec |
E | chkdsk C: /F |
Question 89 |
A | Propagation |
B | Inheritance |
C | Secure Shell |
D | MFA |
E | SSO |
Question 90 |
A | ipconfig /? |
B | ipconfig help |
C | ipconfig man |
D | man ipconfig |
Question 91 |
A | Net timer |
B | Time |
C | Timeset |
D | Net time |
E | Net time set |
Question 92 |
A | Factory reset the gaming consoles. |
B | Configure router QoS engine with service priority for gaming applications. |
C | Replace the router with an upgraded unit. |
D | Reconfigure the gaming consoles' network interfaces. |
E | Power cycle the network appliances. |
F | Replace the IP camera system with a new one. |
Question 93 |
A | Dir |
B | Ping |
C | Ver |
D | MD |
E | CD |
Question 94 |
A | dir |
B | RD |
C | MD |
D | SD |
E | CD |
Question 95 |
A | Identify malware symptoms. |
B | Enable System Restore. |
C | Quarantine infected systems. |
D | Schedule scans and run updates. |
E | Remediate infected systems. |
F | Disable System Restore. |
Question 96 |
A | You can go to BIOS and make the secondary drive as the primary boot drive to download the data. |
B | It would be nearly impossible to recover the user data since the primary drive conating the OS is required to access the seconday drive. |
C | It would be fairly easy as long as the secondary hard drive is not encrpyted. |
D | It would be very difficualt and will require specialized laborotory to recover the data. |
Question 97 |
A | OneDrive |
B | Compatibility mode |
C | Windows Firewall |
D | PowerShell |
Question 98 |
A | chkdsk |
B | diskpart |
C | cleanmgr |
D | defrag |
Question 99 |
A | Call the building supervisor to make sure there is enough solder for others. |
B | Check the temperature at which the solder should be applied. |
C | Consult the MSDS for the solder spool. |
D | Do not attempt to repair a motherboard. It is better to buy a new one. |
Question 100 |
A | Execute the file as3final.py in notepad++ |
B | Open file as3final.py file using the program notepad++ |
C | Append the file name as3final.py to as3final.py by combing notepad and as3final terms. |
D | Change the file name from notepad to as3final.py |
E | Execute the file notepad++ in as3final.py |
Question 101 |
A | Guest |
B | Power user |
C | Administrator |
D | Domain Admin |
Question 102 |
A | Pro |
B | Home |
C | Standard |
D | Enterprise |
Question 103 |
A | Organization security and content policy typically do not apply to executive staff. |
B | Organization security and content policy must follow the legal policies of the country which the company operates. |
C | Organization security and content policy must include explicit punishment guidelines for employees who do not follow the guidelines. |
D | Organization security and content policies are not part of the majority of government organizations. |
E | Organization security and content policy supersede all other legal policies of the country which the company operates. |
Question 104 |
A | Disable logon time restrictions |
B | Block all unused ports on the LAN smart switch |
C | Enforce password complexity |
D | Use the local client certificate for server authentication |
E | Change the default access port |
F | Put the terminal server into the routers DMZ |
Question 105 |
A | Asset ID, MAC address |
B | Location, RFID |
C | Domain name, location, IP address |
D | Domain name, location, asset ID |
Question 106 |
A | Calibrate the touchscreen sensor |
B | Disable and then reenable Bluetooth |
C | Restart the tablet |
D | Disconnect and then reconnect the stylus |
Question 107 |
A | Microsoft |
B | Apple |
C | IBM |
D | CompTIA |
E | WWF |
Question 108 |
A | Brute force |
B | DDoS |
C | Malicious attack |
D | Phishing |
E | Session hijacking |
Question 109 |
A | System Restore |
B | File History |
C | Startup Repair |
D | Windows Registry |
E | Reset Your PC |
Question 110 |
A | Hard reset the cell phone |
B | Reconnect the wireless network connection |
C | Close all running applications |
D | Remove and reinstall the application |
Question 111 |
A | process -del |
B | taskkill |
C | delprocess |
D | deltask |
E | process -k |
Question 112 |
A | Contact the Manager of the company immediately. |
B | Open the folder to investigate the content, but do not open the images. |
C | Open the folder and enjoy the images. |
D | Install the software and ignore the folder. |
E | Ask Sara why she has this type of folder on her work computer. |
Question 113 |
A | spam bot |
B | spyware |
C | trojan |
D | worm |
Question 114 |
A | devmgmt.msc |
B | mtg |
C | MMC |
D | secpol.msc |
E | CMD |
Question 115 |
A | root CA |
B | keys |
C | passwords |
D | tokens |
Question 116 |
A | robocopy |
B | chkdsk /F |
C | tracert /w |
D | diskpart |
Question 117 |
A | Ask the owner to move the files from the server to a local computer |
B | Promptly notify the administrator's immediate supervisor |
C | Rename the folder on the server, and notify the information security officer |
D | Move the folder to another location on the server, and notify the local authorities |
Question 118 |
A | WWAN |
B | WLAN |
C | VLAN |
D | 5G LTE |
E | VPN |
Question 119 |
A | Setup log |
B | Security log |
C | Application log |
D | Tasker log |
E | System log |
Question 120 |
A | Windows 10 |
B | Mac OS |
C | iOS |
D | Android |
E | Ubuntu |
Question 121 |
A | It may result in random reboots. |
B | It may lead to instability issues. |
C | It may interfere with other signed drivers installed on the device. |
D | It may result in damage to the device. |
Question 122 |
A | MBR drive format does not support drives over 4TB while GPT would be able to partition larger drives over 4TB. |
B | MBR can create multiple partitions without any issues but GPT has a limit of four partitions per drive. |
C | MBR is only used by Microsoft products while GPT is only used by Linux and MacOS. |
D | GPT is an older method of partitioning a disk that no longer in used and replaced by MBR. |
Question 123 |
A | MS Excel |
B | CMD |
C | MS Word |
D | MS PowerPoint |
E | Notepad |
Question 124 |
A | Look for program features and the minimum hardware requirements. |
B | Verify that the install is allowed under the company’s licensing agreements. |
C | Read the manual on how HR is going to use the software. |
D | Update the Windows drivers on the computer. |
Question 125 |
A | IP address and domain |
B | Server and gateway |
C | Server and domain |
D | IP address and DNS |
Question 126 |
A | chown |
B | ipaddr /all |
C | ls |
D | ifconfig |
E | ipconfig /all |
Question 127 |
A | 4 GB |
B | 2 GB |
C | 512 MB |
D | 6 GB |
E | 1 GB |
Question 128 |
A | Virus infection of the C drive. |
B | Hyper-Threading has been disabled. |
C | Windows Update is running. |
D | The printing system is running. |
E | Drivers are being downloaded by the Device Manager. |
Question 129 |
A | Ask the customer to find an application that does not use Java. |
B | Delete and clear Java Temporary Internet Files. |
C | Ask the customer to use a different web browser. |
D | Reinstall Java on the affected workstation. |
Question 130 |
A | Boot the workstation in safe mode with Command Prompt and enable Driver Verifier with standard settings |
B | Boot the workstation in safe mode with networking and install the latest stable graphics driver |
C | Boot the workstation in safe mode and disable Windows driver signing requirements |
D | Boot the workstation in safe mode and disable the graphics driver system tray menu |
Question 131 |
A | IPCONFIG |
B | NETDOM |
C | CONVERT |
D | CHKNTFS |
Question 132 |
A | Security Groups |
B | Folder Redirection |
C | Home Folder |
D | Group Policy |
Question 133 |
A | Create a group policy to set minimum password standards. |
B | Display a message on lock screen advising users how importnat to lock their computer. |
C | Set a strong password that requires a renewal every 30 days. |
D | Run a screensaver after one minute of nonuse and a fingerprint lock for after hours. |
E | Apply a screen lock after x minutes of non-use and set login time restrictions for after hours. |
Question 134 |
A | Administrative Tools |
B | Msconfig |
C | Disk Management |
D | Task Manager |
Question 135 |
A | Disable the SSID broadcast. |
B | Install an antivirus on the main server. |
C | Install a firewall and enforce rules. |
D | Disconnect the Internet connection to the LAN. |
E | Install an intrusion detection system (IDS). |
Question 136 |
A | Windows |
B | System32 |
C | boot |
D | Users |
E | Program Files |
Question 137 |
A | Ghost |
B | Image Copy |
C | Robocopy |
D | Sysprep |
E | Image Clone |
Question 138 |
A | Perform a full backup and replace the hard drive |
B | Roll back the OS upgrade. Continue using the older version of Windows |
C | Update the SATA controller driver from the manufacturers website |
D | Reset the PC to its factory conditions. Perform the OS upgrade again |
Question 139 |
A | winload.exe |
B | shell.adb |
C | system32.exe |
D | setup.exe |
E | startup.exe |
Question 140 |
A | Windows user account authentication uses the TPM chipset on the motherboard to encrypt user data. |
B | Windows user account authentication is more secure than BitLocker. |
C | Unlike Windows user accounts, BitLocker is available on multiple platforms such as Ubuntu, iOS and Android. |
D | BitLocker can encrypt hard drives and protect user content from unauthorized access. |
E | Windows user account authentication can only be used with a Windows Server Domain Controller. |
Question 141 |
A | Document your solution. |
B | Move on to the server to a different node or VLAN on the network. |
C | Invoice the customer. |
D | Run a driver update check for the specified software. |
Question 142 |
A | Windows 10 |
B | Windows 98 |
C | iOS |
D | macOS |
E | Android |
Question 143 |
A | Take everyone out to lunch get their mind off of the problem. |
B | Refer your panicking Supervisor and co-workers to professional counseling services. |
C | Quit your job because of this work environment is toxic. |
D | Stay calm and do your job to best of your ability. |
E | Request that you need to speak to a senior Supervisor. |
Question 144 |
A | Before you take any actions, contact the CEO in writing or by email and advise him/her that their IT account is being deleted. |
B | If the IT Manager has the proper authority and documentation, perform the deletion task to the best of your ability. |
C | Contact HR immediately and seek advice. |
D | Before you take any actions, contact the CEO secretly and advise him/her that their IT account is being deleted. |
E | Contact a lawyer as this breaches the professional conduct policies. |
Question 145 |
A | Business processes |
B | End-user acceptance |
C | Plan for change |
D | Backout plan |
E | Risk analysis |
F | Request for proposal |
Question 146 |
A | bash |
B | cat |
C | sbin |
D | ls |
Question 147 |
A | Telnet |
B | VNC |
C | SSH |
D | RDP |
Question 148 |
A | Install grounding bars. |
B | Plug and check if the equipment is working. |
C | Set up dehumidifiers. |
D | Implement a fire suppression system. |
E | Increase the closet's airflow. |
Question 149 |
A | Windows Registry |
B | File Explorer |
C | Device Manager |
D | Task Manager |
E | Services console |
Question 150 |
A | RD |
B | SD |
C | MD |
D | CD |
E | dir |
Question 151 |
A | NTFS |
B | exFAT |
C | FAT16 |
D | FAT32 |
Question 152 |
A | Format command |
B | Disk Management |
C | Computer Management |
D | Disk Cleanup utility |
Question 153 |
A | Task Scheduler |
B | Event Viewer |
C | Task Manager |
D | Services |
Question 154 |
A | A consumer can exchange the apps (applications) between Andorid OS and iOS. |
B | Unlike Android OS, Apple OS allow you to customize the user interface using a system called Launcher. |
C | Both Android OS and iOS can run on almost all handheld modern electronic devices. |
D | Android OS is open source but the iOS is closed source and owned by Apple Inc. |
Question 155 |
A | Task Manager |
B | Mac Management |
C | Time Machine |
D | Force quit |
E | Taskkill |
Question 156 |
A | Task Manager |
B | MMC |
C | Control Panel |
D | Command Prompt |
Question 157 |
A | Msconfig |
B | Chkdsk |
C | System Information |
D | Task Manager |
Question 158 |
A | Domain-level group policies |
B | Local-level user policies |
C | Local-level firewall policies |
D | Network-level firewall policies |
E | Antivirus domain-level policies |
Question 159 |
A | Using msconfig Tools tab. |
B | Using msconfig Services tab. |
C | Using msconfig General tab. |
D | Using msconfig Boot tab. |
Question 160 |
A | User access control |
B | Date and time |
C | UEFI boot mode |
D | Logon times |
Question 161 |
A | Phishing attack |
B | Social engineering |
C | DDoS attack |
D | Brute force attack |
E | Session hijacking attack |
Question 162 |
A | Page-file size |
B | Visual effects |
C | Data execution prevention |
D | Processor scheduling |
Question 163 |
A | Personal license |
B | Volume license |
C | Corporate license |
D | Enterprise license |
E | Open license |
Question 164 |
A | Minimum password length |
B | Minimum password age |
C | Enforce password history |
D | Complexity requirements |
Question 165 |
-Often the website is responding slowly.
-Often the website is unresponsive.
-Some users have problems accessing the website.
-When the webserver is ping from a computer within the same LAN, the ping timeout or the ping time is usually high.
A | DDoS attack |
B | Malicious attack |
C | Brute force attack |
D | HTTP attack |
E | Session hijacking attack |
← |
List |
→ |
| 1 | 2 | 3 | 4 | 5 |
| 6 | 7 | 8 | 9 | 10 |
| 11 | 12 | 13 | 14 | 15 |
| 16 | 17 | 18 | 19 | 20 |
| 21 | 22 | 23 | 24 | 25 |
| 26 | 27 | 28 | 29 | 30 |
| 31 | 32 | 33 | 34 | 35 |
| 36 | 37 | 38 | 39 | 40 |
| 41 | 42 | 43 | 44 | 45 |
| 46 | 47 | 48 | 49 | 50 |
| 51 | 52 | 53 | 54 | 55 |
| 56 | 57 | 58 | 59 | 60 |
| 61 | 62 | 63 | 64 | 65 |
| 66 | 67 | 68 | 69 | 70 |
| 71 | 72 | 73 | 74 | 75 |
| 76 | 77 | 78 | 79 | 80 |
| 81 | 82 | 83 | 84 | 85 |
| 86 | 87 | 88 | 89 | 90 |
| 91 | 92 | 93 | 94 | 95 |
| 96 | 97 | 98 | 99 | 100 |
| 101 | 102 | 103 | 104 | 105 |
| 106 | 107 | 108 | 109 | 110 |
| 111 | 112 | 113 | 114 | 115 |
| 116 | 117 | 118 | 119 | 120 |
| 121 | 122 | 123 | 124 | 125 |
| 126 | 127 | 128 | 129 | 130 |
| 131 | 132 | 133 | 134 | 135 |
| 136 | 137 | 138 | 139 | 140 |
| 141 | 142 | 143 | 144 | 145 |
| 146 | 147 | 148 | 149 | 150 |
| 151 | 152 | 153 | 154 | 155 |
| 156 | 157 | 158 | 159 | 160 |
| 161 | 162 | 163 | 164 | 165 |
| End |
Based on general knowledge and CompTIA guidelines published in 2020.
FAQ | Report an Error
Disclaimer: While every reasonable effort is made to ensure that the information provided is accurate, no guarantees for the currency or accuracy of information are made. It takes several proof readings and rewrites to bring the quiz to an exceptional level. If you find an error, please contact me as soon as possible. Please indicate the question ID-Number or description because server may randomize the questions and answers.