← Exams and Quizzes | Professional Exams →
Notice
If you get a question wrong, you can still click on the other answers. This will open up hints and explanations (if available), which will provide additional information. Exam should be 1 minute per question and please time accordingly.It is not required to have CompTIA A+ certification prior to obtaining CompTIA Network+ certification. It is recommended to have CompTIA A+ certification or the knowledge of the subject matter that is covered under A+ certification exam before taking Network+ certification exam. It is also recommended, but not required, that you have about 12 months of IT networking work experience.
Go to: Set I | Set III
CompTIA Network+ N10-007 - Set II
Congratulations - you have completed CompTIA Network+ N10-007 - Set II.
You scored %%SCORE%% out of %%TOTAL%%. With incorrect multiple attempts, your score is %%PERCENTAGE%%. Your performance has been rated as %%RATING%%
Question 1 |
A | Social engineering |
B | Session hijacking |
C | ARP poisoning |
D | Evil twin |
E | DHCP exhaustion |
Question 2 |
A | Motion sensors |
B | Sign-in sheets |
C | Swipe badges |
D | Video cameras |
Question 3 |
A | Plenum |
B | PVC |
C | Single-mode |
D | Cat 7 |
Question 4 |
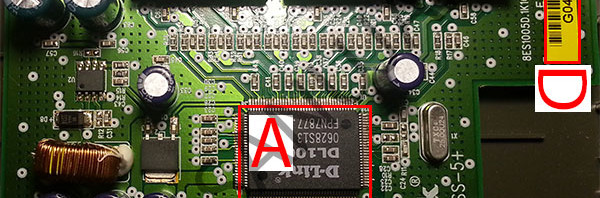
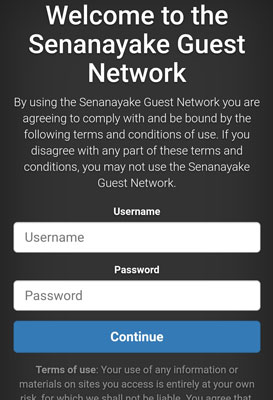
A | Captive portal |
B | MAC filtering |
C | SSL certificate |
D | EAP-TLS |
E | WPA2 |
Question 5 |
A | -i address |
B | /all |
C | eth_addr |
D | -a |
Question 6 |
A | Server room |
B | Intermediate distribution frame |
C | Equipment closet |
D | Demarcation point |
Question 7 |
A | Disable the SMTP service on the server |
B | Disable FTP service on the server |
C | Disable Telnet service on the server |
D | Disable DHCP service on the server |
Question 8 |
A | Synchronization of clocks over a computer network |
B | Retrieving contents of an Internet page from a web server |
C | Monitoring of network-attached devices |
D | Allocation of IP addresses |
Question 9 |
A | Connect the legacy devices with a PSK while the modern devices should use the more secure EAP. |
B | Create two SSIDs, one to support CCMP-AES encryption and one with TKIP-RC4 encryption. |
C | Configure modern devices under the 5GHz band while dedicating the 2.4GHz band to legacy devices. |
D | Configure the APs to use LEAP authentication to support WPA rather than WPA2 for full compatibility. |
Question 10 |
A | Fiber Channel |
B | vSAN |
C | FCoE |
D | VPC |
E | Virtual switch |
Question 11 |
A | Speed |
B | Duplex |
C | TTL |
D | MTU |
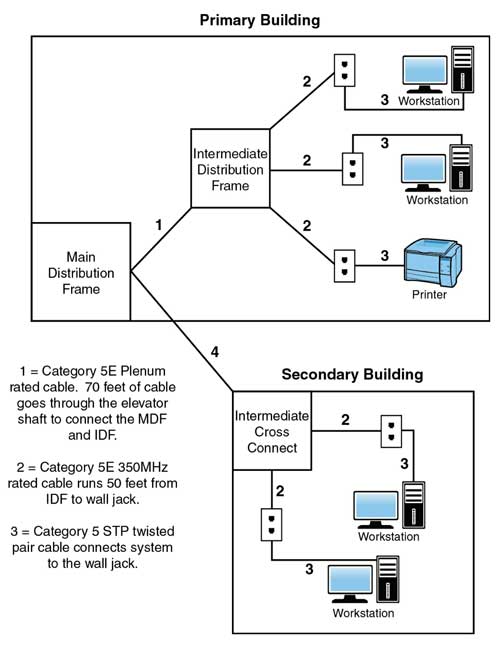
Question 12 |
A | None, the network looks good. |
B | Cable 3 should be an STP cable. |
C | Cable 1 does not need to be plenum rated. |
D | Cable 2 should be an STP cable. |
Question 13 |
A | SSL |
B | SSH |
C | FTP |
D | SNMP |
E | CHAP |
Question 14 |
A | Misconfigured VLSM |
B | Rogue DHCP server |
C | Expired IP address |
D | Exhausted dynamic scope |
Question 15 |
A | IDF/MDF documentation |
B | Physical diagram |
C | Performance baseline |
D | Change management |
Question 16 |
A | Motion detectors |
B | Video surveillance |
C | Biometric scanners |
D | Door locks |
Question 17 |
A | Adding a fingerprint reader and retina scanner |
B | Using a smart card and RSA token |
C | Enforcing a stronger password policy and using a hand geometry scan |
D | Adding a fingerprint reader to each workstation and providing a RSA authentication token |
Question 18 |
A | Review and modify the firewall rules |
B | Verify the default passwords have been changed |
C | Upgrade to the latest firmware |
D | Generate new SSH keys |
Question 19 |
A | Plug in to another port |
B | Change the switch |
C | Replace the NIC |
D | Modify the speed and duplex |
Question 20 |
A | OTDR |
B | Multimeter |
C | Packet sniffer |
D | Spectrum analyzer |
Question 21 |
route add 0.0.0.0 mask 0.0.0.0 192.169.1.222 metric 1
A | The technician is adding a static IP address. |
B | The technician is setting the default gateway. |
C | The technician is clearing the subnet mas setting. |
D | The technician is clearing the route table. |
Question 22 |
A | Differential |
B | Snapshots |
C | Replica |
D | Incremental |
Question 23 |
A | Media type |
B | Room number |
C | Rack location |
D | Hostname |
Question 24 |
A | Firewall |
B | Wireless access point |
C | Network switch |
D | Router |
E | Media converter |
Question 25 |
A | BRI |
B | SVC |
C | SNR |
D | RFI |
Question 26 |
A | Proxy service |
B | Dynamic DNS |
C | Intrusion detection |
D | Content filtering |
Question 27 |
A | Reset the two-factor token. |
B | Disable unused ports. |
C | Disable virtual ports. |
D | Upgrade the firmware. |
Question 28 |
“The Security certificate presented by this website was not trusted by trusted certificate authority.”
Sanuja has cleared his cache and cookies, rebooted his machine, and attempted to browse to the website from a coworker’s desktop, but it still presented with this error. Which of the following is the MOST likely cause of this error?
A | The web server is missing an intermediate certificate. |
B | The website is missing an HTTPS certificate. |
C | The SSL certificate has expired. |
D | TLS is not enabled in the browser. |
Question 29 |
A | The cable is damaged |
B | The cable has bent pins |
C | The cable is rollover cable |
D | The cable is a crossover cable |
E | The cable is a Cat 5 cable |
Question 30 |
A | AES-CCMP |
B | EAP-TLS |
C | WEP-TKIP |
D | WPA-PSK |
Question 31 |
A | DNS sinkhole |
B | DDoS |
C | MITM |
D | IDS firewall |
E | DDoS |
Question 32 |
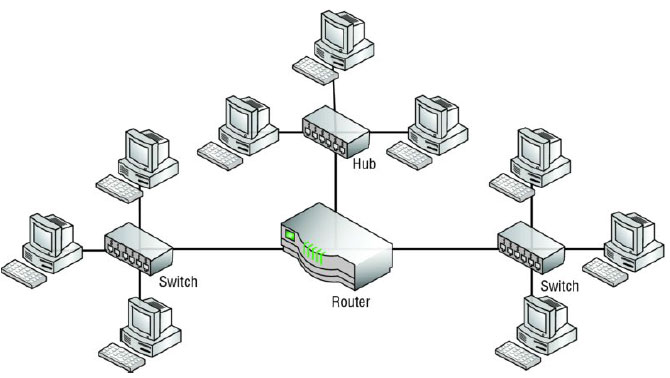
A | There are three collision domains and one broadcast domain. |
B | There are nine collision domains and three broadcast
domains. |
C | There are seven collision domains and three broadcast
domains. |
D | There are three collision domains and three broadcast
domains. |
E | There is one collision domain and one broadcast domain. |
Question 33 |
A | None of the answers are correct. |
B | UDP |
C | TCP |
D | IP |
E | Ethernet |
Question 34 |
A | Implement a standardized UNC |
B | Label existing systems with current hostnames |
C | Enforce port security to require system authentication |
D | Forward the DHCP logs to the security manager every day |
Question 35 |
A | DHCP |
B | SCP |
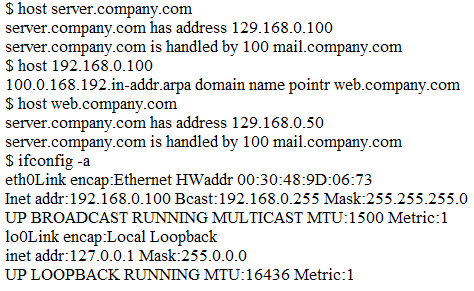
C | FTP |
D | TFTP |
E | Telnet |
Question 36 |
A | VLAN hopping |
B | Session hijacking |
C | Bluesnarfing |
D | MAC spoofing |
E | Man-in-the-middle |
Question 37 |
A | Loopback adapter |
B | Cable tester |
C | Multimeter |
D | Tone generator |
Question 38 |
A | InfiniBand |
B | FCoE |
C | OC3 |
D | iSCSI |
Question 39 |
A | Port mirroring |
B | Trunking |
C | Spanning tree |
D | Port aggregation |
Question 40 |
A | 802.3af |
B | 802.3at |
C | 802.1q |
D | 802.11ac |
E | 802.1X |
Question 41 |
A | Layer 2 switch |
B | Cable modem |
C | DNS server |
D | SOHO router |
Question 42 |
A | SMB |
B | NTP |
C | SNMP |
D | SSL |
E | RDP |
Question 43 |
A | Key escrow |
B | CSR |
C | OCSP |
D | CRL |
Question 44 |
A | Ports 80 and 443 |
B | Ports 67 and 68 |
C | Ports 56 and 57 |
D | Port 123 and 8080 |
E | Ports 20 and 21 |
Question 45 |
A | 12 |
B | 13 |
C | 3 |
D | 15 |
E | 14 |
Question 46 |
A | Replace the server's single-mode fiber cable with multimode fiber |
B | Move the fiber cable to a different port on the switch where both strands function |
C | Use a TDR to test both strands of a new replacement cable prior to connecting it to the server |
D | Reverse the fiber strands of the cable and reconnect them to the server |
Question 47 |
A | Port 110 |
B | Port 22 |
C | Port 110 |
D | Port 80 |
E | Port 443 |
Question 48 |
A | Implement stacking on the switches in the rack |
B | Add a redundant power supply to the switch |
C | Add a second UPS into the rack |
D | Install a power converter for the switch |
Question 49 |
A | ipconfig |
B | nslookup |
C | dig |
D | arp |
Question 50 |
A | Application |
B | Transport |
C | Physical |
D | Network |
Question 51 |
A | Require PEAP for authentication to the wireless network |
B | Use MAC filtering for authorization to the wireless network |
C | Implement a Faraday cage within the building premises |
D | Require a pre-shared key for authentication to the wireless network |
Question 52 |
A | Set the AP to half-duplex to compensate for signal loss |
B | Install a repeater to boost the signal to its destination |
C | Upgrade the cable from Cat 5 to Cat 5e or Cat 6 |
D | Replace the UTP cable with plenum cable |
Question 53 |
A | Incident response |
B | AUP |
C | Offboarding |
D | Remote access |
E | DLP |
Question 54 |
A | permit tcp any any eq 110 |
B | permit udp any any eq 25 |
C | permit tcp any any eq 8080 |
D | permit udp any any eq 68 |
E | permit tcp any any eq 20 |
F | permit udp any any eq 53 |
Question 55 |
A | traceroute |
B | Nmap |
C | netstat |
D | pathping |
Question 56 |
A | dig |
B | tcpdump |
C | arp |
D | nmap |
Question 57 |
A | There is one collision domain for this network. |
B | There are 3 collision domains, one for each switch-to-switch connection. |
C | There are 9 collision domains, one for each half-duplex connection. |
D | There are 12 collision domains, one for each switch connection. |
Question 58 |
A | Hub |
B | Router |
C | Bridge |
D | Switch |
Question 59 |
A | Spam |
B | Ransomware |
C | Man-in-the-middle |
D | Phishing |
Question 60 |
A | Coaxial cabling |
B | STP cabling |
C | UTP cabling |
D | Fiber-optic cabling |
Question 61 |
A | 192.168.12.97 to 255.255.255.192 |
B | 192.168.12.97 to 255.255.255.248 |
C | 192.168.12.97 to 255.255.255.224 |
D | 192.168.12.97 to 255.255.255.240 |
Question 62 |
A | Establish a plan of action |
B | Gather information |
C | Document the findings |
D | Determine the symptoms |
Question 63 |
Image Credits: https://www.homedepot.com/p/ Ideal-Punchdown-Tool- with-110-and-66- Blades-35-485/ 203761571
A | Tone generator and locator |
B | Crimper |
C | Punchdown tool |
D | Butt set |
Question 64 |
A | 6 |
B | 12 |
C | 2 |
D | 1 |
E | 0 |
Question 65 |
A | NDA |
B | SLA |
C | DLP |
D | AUP |
Question 66 |
A | Partial mesh |
B | Ad hoc |
C | Bus |
D | Ring |
Question 67 |
A | nbtstat |
B | netstat |
C | nslookup |
D | pathping |
Question 68 |
A | AUP |
B | BYOD |
C | MOU |
D | NDA |
Question 69 |
A | 900MHz |
B | 2.4 GHz |
C | 5GHz |
D | 56MHz |
Question 70 |
A | DNS |
B | ICMP |
C | DHCP |
D | HTTP |
E | LADP |
Question 71 |
A | 240 private networks |
B | 48 collision domains, 5 broadcast domains |
C | 48 networks, 5 segments |
D | 240 usable IP addresses |
E | 5 collision domains, 48 segments |
Question 72 |
A | The Faraday cage is creating latency on the cellular network. |
B | The Faraday cage is creating attenuation of the cellular network. |
C | The Faraday cage is creating interference within the bookstore. |
D | The Faraday cage prevents access by redirecting signals. |
Question 73 |
A | Two routers with each router connected to a 12-port switch, with a firewall connected to the switch connected to the manager's desktop computers, VoIP phones, and printer |
B | One router connected to one 12-port switch configured for the manager's computers, phones, and printer, and one 12-port switch configured for the other computers, VoIP phones, and printer |
C | One router connected to one 24-port switch configured with two VLANS: one for the manager's computers, VoIP phones, and printer, and one for the other computers, VoIP phones, and printer |
D | One router connected to one 24-port switch configured with three VLANS: one for the manager's computers and printer, one for the other computers and printer, and one for the VoIP phones |
Question 74 |
A | Duplicate IP addresses |
B | APIPA address |
C | Duplicate MAC addresses |
D | Loopback address |
Question 75 |
A | Implementing a modem on the AUX port to access a network device. |
B | Accessing a DSL router via the console port. |
C | Telnet into the router over a secure VPN. |
D | Using a secure SSH connection over the WAN link to connect to a server. |
Question 76 |
A | 1024 |
B | 2046 |
C | 512 |
D | 2048 |
E | 1022 |
F | 510 |
Question 77 |
A | authpriv |
B | SHA |
C | Authentication passphrase |
D | MD5 |
Question 78 |
IP: 192.168.1.100
Mask: 255.255.255.0
Router: 192.168.1.1
A | Security type mismatch |
B | Wrong SSID |
C | Interference |
D | Channel overlap |
Question 79 |
A | PRI |
B | MPLS |
C | ISDN |
D | Frame relay |
E | Broadband cable |
Question 80 |
A | risk assessment. |
B | penetration testing. |
C | device hardening. |
D | role separation. |
Question 81 |
A | Inventory report |
B | Labeling report |
C | Network diagrams |
D | Change management |
Question 82 |
A | Adding a router reduces the amount of unicast traffic on each of the two LANs. |
B | Adding a router prevents computers on one LAN from communicating with computers on another LAN. |
C | Adding a router reduces the amount of broadcast traffic on each of the two LANs. |
D | Adding a router diverts traffic to an alternate path through the network. |
Question 83 |
A | PEAP |
B | Captive portal |
C | EAP-TLS |
D | WP2-PSK |
Question 84 |
A | PPP |
B | Fibre Channel |
C | iSCSI |
D | RDMA |
Question 85 |
A | iSCSI |
B | Port aggregation |
C | Jumbo frames |
D | QoS tags |
Question 86 |
A | Wardriving |
B | MITM attack |
C | Session hijacking |
D | DDoS attack |
E | Spoofing attack |
Question 87 |
A | DNS SRV record |
B | Host-based firewall settings |
C | Server IP address |
D | TACAS+ server time |
Question 88 |
Gigabit Ethernet 1 Interface: 10.10.0.1/24 Serial 0 Interface: 10.10.0.253/30
A | The router was configured with an incorrect IP address |
B | The router was configured with an incorrect default gateway |
C | The router was configured with an incorrect loopback address |
D | The router was configured with an incorrect subnet mask |
Question 89 |
A | 10.5.4.0/22 |
B | 10.233.2.0/23 |
C | 192.168.25.0/24 |
D | 172.18.0.0/23 |
E | 172.16.0.0/22 |
Question 90 |
A | Crosstalk |
B | Bad port |
C | ACL misconfiguration |
D | Duplex/speed mismatch |
Question 91 |
A | Proxy server |
B | Router |
C | Load balancer |
D | Switch |
Question 92 |
A | EMI |
B | Open/short |
C | TX/RX reverse |
D | Attenuation |
Question 93 |
A | The use of autonomous APs with a wireless controller |
B | The use of autonomous APs with a load balancer |
C | The use of lightweight APs with a load balancer |
D | The use of lightweight APs with a wireless controller |
Question 94 |
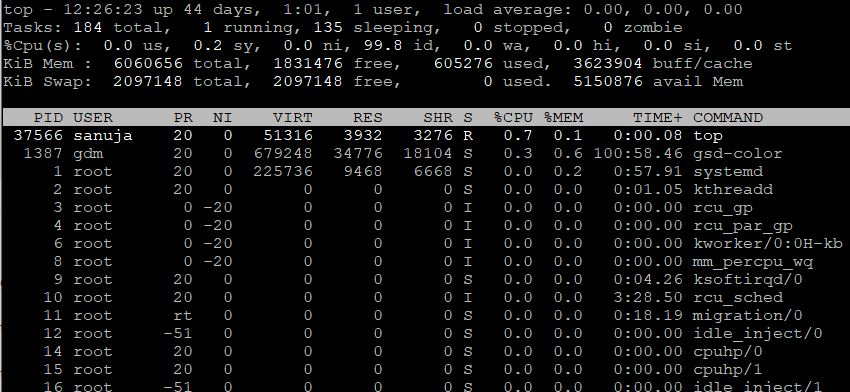
A | systemd |
B | top |
C | sanuja |
D | gdm |
E | root |
Question 95 |
A | Point-to-multipoint |
B | Point-to-point |
C | Site-to-site |
D | Client-to-site |
Question 96 |
A | Biometric device |
B | Video camera |
C | Proximity reader |
D | Identification card |
Question 97 |
A | Disable the SSID broadcast on each access point. |
B | Enable MAC address filtering on each access point. |
C | Reduce the TX power on each access point. |
D | Enable AP isolation on each access point. |
Question 98 |
A | MITM |
B | DDoS |
C | Phishing |
D | Evil twin |
E | OCSP stapling |
Question 99 |
A | Single sign-on |
B | TACACS+ |
C | Captive portal |
D | RADIUS |
Question 100 |
A | Broadband |
B | Baseband |
C | CSMA |
D | Analog modem |
Question 101 |
A | Perform file hashing |
B | Generate new keys |
C | Change default credentials |
D | Update firmware |
Question 102 |
A | Configure the DNS address in the DHCP scope to a 10.10.5.0/24 address. |
B | Verify the host has physical connectivity and is on the correct VLAN. |
C | Change the IP scope on the DHCP server to a public IP address range. |
D | Perform a traceroute command to identify the router that is not functioning. |
Question 103 |
A | Bridge |
B | Domain server |
C | Signal repeater |
D | Layer 2 switch |
E | Layer 3 switch |
Question 104 |
A | 2001:0:d58::95:7565:1 |
B | 2001:0:d58:0:0:95:7565:1 |
C | 2001::d58::95:7565:1 |
D | 2001:0:0d58::95:7565:1 |
Question 105 |
A | DHCP |
B | Dynamic routes |
C | Routing table |
D | Routing loop |
E | Route redistribution |
Question 106 |
A | Reviewing SLA requirements |
B | Reviewing application logs |
C | Reviewing a baseline report |
D | Reviewing a vulnerability scan |
Question 107 |
A | Credentials |
B | VNC application |
C | Geotagging application |
D | Kerberos |
Question 108 |
A | Replacing the management software's self-signed certificate with a valid certificate |
B | Changing the management software's default port |
C | Disabling unnecessary services from the server and management software |
D | Changing the management software's default credentials |
Question 109 |
A | Port 161 |
B | Port 123 |
C | Port 25 |
D | Port 69 |
Question 110 |
A | Telnet |
B | FTPS |
C | SFTP |
D | TFTP |
E | SSL |
Question 111 |
A | Secure the area |
B | Document the scene |
C | Take pictures upon arrival |
D | Implement a chain of custody |
Question 112 |
A | public/private networks |
B | network devices |
C | packet flow |
D | traffic-routing protocols |
Question 113 |
A | Spoofing attacks require physical presence |
B | DDoS attacks are launched from multiple hosts |
C | DDoS attacks target multiple networks |
D | Spoofing attacks originate from a single host |
Question 114 |
A | Enables remote login and command execution. |
B | It cannot be used on modern Windows computers. |
C | It does not provide authentication. |
D | Provides username & password authentication. |
E | Transmits data in an unencrypted form. |
F | Encrypts network connection. |
Question 115 |
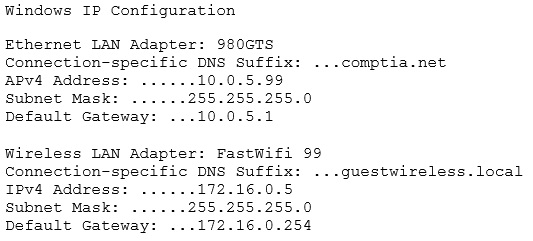
Which of the following would MOST likely allow the network drives to be accessed?
A | Check the wireless DHCP configuration |
B | Disable the WLAN adapter |
C | Update the WLAN adapter driver |
D | Disable the LAN adapter |
Question 116 |
A | Transport |
B | Presentation |
C | Data link |
D | Session |
Question 117 |
A | IPSec |
B | PPTP |
C | SSL VPN |
D | PTP |
Question 118 |
A | The technician should reset all the phones and deprovision information from the provider |
B | The technician should check the internal diagnostics on all the phones to look for a common thread |
C | The technician should use a packet tracer to see if the traffic is getting out of the network |
D | The technician should run ping tests on the Internet line to monitor for packet loss and latency |
Question 119 |
A | Implement preventive measures |
B | Question users |
C | Establish a theory of probable cause |
D | Document findings |
E | Test solutions |
F | Duplicate the problem |
Question 120 |
A | Additional lease time for the laptop computers |
B | CNAME record in the users dynamic DNS accounts |
C | IP helper relay system for configuration hops |
D | DHCP reservation for the laptops MACs |
Question 121 |
-WLAN architecture supporting speeds in excess of 150 Mbps
-Client less remote network access
-Port-based network access control
A | 802.11n, SSL-VPN, 802.1x |
B | 802.11b, PPTP,802.1x |
C | 802.11ac, MPLS, 802.3 |
D | 802.11g, MS-CHAP, 802.16 |
E | 802.11a, IPSec VPN, 802.1x |
Question 122 |
A | ICMP |
B | RTP |
C | SIP |
D | SMB |
E | H.323 |
F | NTP |
Question 123 |

Which of the following ones should the technician use to place the webserver and which of the following firewall rules should the technician configure?
A | Place the web server in the DMZ with an inbound rule from eth1 interface to eth0 to accept traffic over port 80 designated to the webserver |
B | Place the web server in the private zone with an inbound rule from eth2 interface to eth1 to accept traffic over port 80 designated to the webserver |
C | Place the web server in the public zone with an inbound rule from eth0 interface to accept traffic over port 80 designated to the webserver |
D | Place the web server in the DMZ with an inbound rule from eth0 interface to eth1 to accept traffic over port 80 designated to the webserver |
Question 124 |
A | The R&D department should have 172.16.49.207 as a broadcast address. |
B | The marketing department should have usable IPs ranging from 172.16.49.129 to 172.16.49.190. |
C | The R&D department should receive a /27 network. |
D | The marketing department should receive a /25 network. |
E | The legal department should have a first usable IP address of 172.16.49.190. |
F | The legal department should have usable IPs ranging from 172.16.49.129 to 172.16.49.190. |
G | The finance department should have 172.16.49.127 as a broadcast address. |
H | The R&D department should have a last usable IP address of 172.16.49.190. |
Question 125 |
A | IP helper |
B | DNS record type |
C | Ping table |
D | DHCP lease time |
E | TTL |
Question 126 |
A | HTTP |
B | NetBIOS |
C | DNS |
D | DHCP |
E | ICMP |
Question 127 |
A | ipconfig /all |
B | ipconfig /release |
C | ipconfig /flushdns |
D | ipconfig /renew |
Question 128 |
A | The LAN and WLAN should be configured in the same zone with dynamic DENY ALL rules. |
B | The LAN and WLAN should be marked as trusted during work hours and untrusted during off hours. |
C | The LAN and WLAN should be configured in the DMZ so traffic is denied automatically. |
D | The LAN and WLAN should be configured in separate zones with a firewall in between. |
Question 129 |
A | 10.8.0.0/19 |
B | 10.0.0.0/24 |
C | 10.8.0.0/16 |
D | 10.8.0.0/20 |
Question 130 |
A | Packet sniffer |
B | nslookup |
C | Spectrum analyzer |
D | netstat |
Question 131 |
A | Network mapper |
B | WAP power level controls |
C | Protocol analyzer |
D | Logical network diagram |
Question 132 |
A | Bent pins |
B | VLAN mismatch |
C | Duplex mismatch |
D | TX/RX reverse |
E | Damaged cables |
F | Crosstalk |
Question 133 |
A | It segments broadcast domains in the network infrastructure |
B | It provides multiple collision domains on one switchport |
C | It provides multiple broadcast domains within a single collision domain |
D | It provides a faster port to all servers |
Question 134 |
A | Create a port location diagram |
B | Create a network baseline |
C | Create a rack diagram |
D | Create an inventory database |
Question 135 |
A | The utility company throttles power during peak hours |
B | There is additional data being transferred over the wireless network |
C | An IoT device is causing a DoS attack on the wireless network |
D | There is interference with the smart reader |
Question 136 |
A | Layer 3 – Network |
B | Layer 1 – Physical |
C | Layer 7 – Application |
D | Layer 6 - Presentation |
E | Layer 4 – Transport |
Question 137 |
A | Duplex/Speed mismatch |
B | VLAN mismatch |
C | Duplicate IP address |
D | TX/RX reverse |
Question 138 |
A | OID |
B | OTDR |
C | SNMP host |
D | SNMP agent |
E | OUI |
Question 139 |
A | MAC filtering |
B | Open wireless |
C | Geofencing |
D | Pre-shared key |
Question 140 |
A | SRV |
B | AAAA |
C | CNAME |
D | MX |
Question 141 |
A | Attenuation |
B | Jitter |
C | Frequency mismatch |
D | Latency |
Question 142 |
A | Bridge |
B | Layer 3 switch |
C | Load balancer |
D | Layer 2 switch |
Question 143 |
A | Content filter |
B | Wireless controller |
C | RADIUS server |
D | VoIP PBX |
Question 144 |
A | Demarc |
B | IDF |
C | Data tier |
D | DMZ |
Question 145 |
A | IEEE 802.1X |
B | IEEE 802.11ac |
C | IEEE 802.3x |
D | IEEE 802.1q |
Question 146 |
A | TLS |
B | SFTP |
C | SSH |
D | LDAP |
Question 147 |
A | Because a secure firewall will protect the device |
B | Because FTP is not a secure service |
C | Because SCP is not a secure service |
D | Because secure protocols would reject malicious packets |
Question 148 |
A | Move the straight-through Ethernet cable connecting the switches to the first port on both switches. |
B | Replace the new switch with a hub to ensure Layer1 connectivity on the new network segment. |
C | Add a second cable connecting the switches for redundancy and disabling STP on both switches. |
D | Connect the switches with a cable that has a TIA/EIA 586A wired connector end and a TIA/EIA 586B wired end. |
Question 149 |
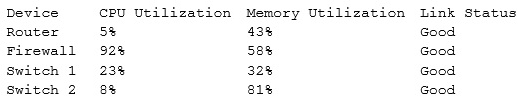
Which of the following devices is causing the issue?
A | Switch 1 |
B | Firewall |
C | Router |
D | Switch 2 |
Question 150 |
Subnet 1: 192.168.1.0/26
Subnet 2: 192.168.1.65/26
Company B uses the following scheme:
Subnet 1: 192.168.1.50/28
A | DMZ |
B | PAT |
C | NAT |
D | VLAN |
Question 151 |
A | Star |
B | Ad hoc |
C | Ring |
D | Mesh |
Question 152 |
A | CNAME |
B | MX |
C | PTR |
D | A |
E | NS |
Question 153 |
A | 1000BaseLX SFP |
B | Duplex GBIC |
C | Duplex SFP+ |
D | Bidirectional SFP |
Question 154 |
A | One of the wireless access points is on the wrong frequency |
B | Distance limitations are preventing the students from connecting |
C | The students are using more than one wireless device port seat |
D | The students are attempting to connect 802.11g devices |
Question 155 |
A | Loop protection is enabled on the root port of a switch. |
B | BPDUs entering the root bridge are ignored. |
C | The STP root bridge cannot be changed. |
D | Broadcast storms entering from a root port are blocked. |
Question 156 |
A | Load balancer |
B | Proxy server |
C | VPN concentrator |
D | IDS |
E | IPS |
Question 157 |
A | Cat 3 |
B | RG-6 |
C | Cat 6 |
D | Cat 5 |
E | SMF |
Question 158 |
A | Multilayer switch |
B | Switch |
C | Next-generation firewall |
D | Bridge |
Question 159 |
A | Backs up files with the archive bit set but does not clear the bit. |
B | Backs up all files and sets the archive bit. |
C | Backs up files with a date earlier than today’s date with a clear archive bit. |
D | Backs up files with the creation or modified date as the current date. |
Question 160 |
A | NAS |
B | SAN |
C | SaaS |
D | IaaS |
Question 161 |
User A
IP address: 192.168.1.121
Subnet mask: 255.255.255.0
Default gateway: 192.168.1.1
User B
IP address: 192.168.1.125
Subnet mask: 255.255.248.0
Default gateway: 192.168.1.1
A | The subnet values should be the same |
B | User B's IP address is not a loopback address |
C | The default gateway should have different values |
D | There is no problem identifiable by the values given. |
Question 162 |
A | Load balancer |
B | Clustering |
C | TCP offloading |
D | Round robin |
E | Jumbo frames |
Question 163 |
A | TDR |
B | Loopback adapter |
C | Spectrum analyzer |
D | OTDR |
Question 164 |
A | MOU |
B | NDA |
C | AUP |
D | SLA |
Question 165 |
A | Implement the solution |
B | Do nothing |
C | Escalate the ticket to a senior technician |
D | Document the findings and outcomes |
E | Establish a theory of probable cause |
Question 166 |
A | Channel 7 |
B | Channel 9 |
C | Channel 6 |
D | Channel 10 |
Question 167 |
A | Clustering |
B | Load balancing |
C | NIC teaming |
D | Multiple NAT |
E | Redundant circuits |
Question 168 |
A | Protocol analyzer |
B | Tone generator |
C | Spectrum analyzer |
D | Multimeter |
E | OTDR |
Question 169 |
A | Server-based firewall configuration issue |
B | DHCP scope availability |
C | VLAN routing |
D | Patch cable type |
Question 170 |
A | Incident response policy |
B | Data loss prevention |
C | Licensing restrictions |
D | Remote access policies |
E | International export controls |
Question 171 |
A | The ports do not belong to a live system |
B | The ports are associated with deprecated services |
C | The ports replied with a SYN/ACK response |
D | The ports belong to an active system and are denying requests |
Question 172 |
A | Use a TFTP server and UDP protocol. |
B | Use an FTP server and provide the file hash. |
C | Use a modem and dial-up connection. |
D | Use an HTTP server to share the file. |
Question 173 |
A | Reverse the wires leading to pins 2 and 3 |
B | Reverse the wires leading to pins 1 and 3 |
C | Reverse the wires leading to pins 1 and 2 |
D | Reverse the wires leading to pins 2 and 4 |
Question 174 |
A | Data loss prevention |
B | Acceptable use |
C | Incident response |
D | Asset disposal |
Question 175 |
A | Packet filtering utility |
B | MS Windows command-line tool |
C | Packet tracing utility |
D | Linux command-line tool |
E | Packet capturing utility |
Question 176 |
A | NAC |
B | SSO |
C | RADIUS |
D | Kerberos |
E | MFA |
F | Certificate |
Question 177 |
A | Spanning tree |
B | Flood guard |
C | DHCP snooping |
D | BPDU guard |
Question 178 |
A | SIP |
B | DSCP |
C | STP |
D | VLANs |
Question 179 |
A | MAC reservation |
B | DHCP timer |
C | Lease time |
D | Pool |
E | IP helper |
Question 180 |
A | Segments |
B | Frames |
C | Datagrams |
D | Packets |
Question 181 |
A | RJ45 |
B | DB-9 |
C | SFTP |
D | SC |
E | LC |
F | GBIC |
Question 182 |
A | Digital signatures |
B | Digital signatures |
C | SSL certificate |
D | 3DES encryption |
Question 183 |
A | DHCP |
B | DNS |
C | TCP/IP |
D | SQL |
Question 184 |
A | Create a VLAN for all unused switchports. |
B | Create a honeypot to attract attackers. |
C | Implement a DMZ for all external services. |
D | Implement root guard on all switches. |
Question 185 |
A | Tone generator |
B | Punchdown tool |
C | Loopback adapter |
D | Multimeter |
Question 186 |
A | Session hijacking |
B | Trojan horse |
C | Social engineering |
D | Logic bomb |
E | Insider threat |
Question 187 |
A | Cat 6a |
B | Cat 5e |
C | Cat 6 |
D | Cat 7 |
Question 188 |
A | SFTP |
B | EAP-PEAP |
C | RDP set to console connection |
D | SSH in tunnel mode |
Question 189 |
A | SFP |
B | GBIC |
C | SPF |
D | MDI-X |
E | ASIC |
Question 190 |
A | Activate MAC address filtering. |
B | Change the WiFi password. |
C | Disable the SSID broadcast. |
D | Implement WEP authentication. |
Question 191 |
A | Samba |
B | Telnet |
C | TFTP |
D | LDAP |
Question 192 |
A | Access point |
B | DOCSIS modem |
C | Demarc |
D | DSL modem |
E | Wireless router |
Question 193 |
A | Rack diagram |
B | Network diagram |
C | Network configuration |
D | Change management |
Question 194 |
A | Telnet over PSTN |
B | RDP over SSLv2 HTTPS terminal services gateway |
C | SSH over IPsec client-to-site VPN |
D | HTTP over WPA2-TKIP WiFi |
Question 195 |
A | There is no reverse DNS entry for this host |
B | The reverse DNS entry is pointing to a different host |
C | The server IP address is incorrectly configured |
D | The DNS lookup entry is incorrectly configured |
Question 196 |
A | 10Base2 |
B | 1000BaseSX |
C | 1000BaseT |
D | 10Base5 |
E | 10GBaseT |
F | 1000BaseLX |
Question 197 |
A | Switch configuration |
B | Damaged cable |
C | Attenuation |
D | Incorrect pin-out |
Question 198 |
A | Star |
B | Bus |
C | Mesh |
D | Ring |
Question 199 |
A | Crosstalk |
B | Open/short on the cable |
C | Jitter |
D | Transceiver mismatch |
Question 200 |
A | 802.11n |
B | 802.11b |
C | 802.11ac |
D | 802.11a |
← |
List |
→ |
| 1 | 2 | 3 | 4 | 5 |
| 6 | 7 | 8 | 9 | 10 |
| 11 | 12 | 13 | 14 | 15 |
| 16 | 17 | 18 | 19 | 20 |
| 21 | 22 | 23 | 24 | 25 |
| 26 | 27 | 28 | 29 | 30 |
| 31 | 32 | 33 | 34 | 35 |
| 36 | 37 | 38 | 39 | 40 |
| 41 | 42 | 43 | 44 | 45 |
| 46 | 47 | 48 | 49 | 50 |
| 51 | 52 | 53 | 54 | 55 |
| 56 | 57 | 58 | 59 | 60 |
| 61 | 62 | 63 | 64 | 65 |
| 66 | 67 | 68 | 69 | 70 |
| 71 | 72 | 73 | 74 | 75 |
| 76 | 77 | 78 | 79 | 80 |
| 81 | 82 | 83 | 84 | 85 |
| 86 | 87 | 88 | 89 | 90 |
| 91 | 92 | 93 | 94 | 95 |
| 96 | 97 | 98 | 99 | 100 |
| 101 | 102 | 103 | 104 | 105 |
| 106 | 107 | 108 | 109 | 110 |
| 111 | 112 | 113 | 114 | 115 |
| 116 | 117 | 118 | 119 | 120 |
| 121 | 122 | 123 | 124 | 125 |
| 126 | 127 | 128 | 129 | 130 |
| 131 | 132 | 133 | 134 | 135 |
| 136 | 137 | 138 | 139 | 140 |
| 141 | 142 | 143 | 144 | 145 |
| 146 | 147 | 148 | 149 | 150 |
| 151 | 152 | 153 | 154 | 155 |
| 156 | 157 | 158 | 159 | 160 |
| 161 | 162 | 163 | 164 | 165 |
| 166 | 167 | 168 | 169 | 170 |
| 171 | 172 | 173 | 174 | 175 |
| 176 | 177 | 178 | 179 | 180 |
| 181 | 182 | 183 | 184 | 185 |
| 186 | 187 | 188 | 189 | 190 |
| 191 | 192 | 193 | 194 | 195 |
| 196 | 197 | 198 | 199 | 200 |
| End |
Based on general knowledge and CompTIA guidelines published in 2020.
FAQ | Report an Error
Study outline at: CompTIA Exams Guide
Disclaimer: While every reasonable effort is made to ensure that the information provided is accurate, no guarantees for the currency or accuracy of information are made. It takes several proof readings and rewrites to bring the quiz to an exceptional level. If you find an error, please contact me as soon as possible. Please indicate the question ID-Number or description because server may randomize the questions and answers.