← Exams and Quizzes | Professional Exams →
Notice
If you get a question wrong, you can still click on the other answers. This will open up hints and explanations (if available), which will provide additional information. Exam should be 1 minute per question and please time accordingly.It is not required to have CompTIA A+ certification prior to obtaining CompTIA Network+ certification. It is recommended to have CompTIA A+ certification or the knowledge of the subject matter that is covered under A+ certification exam before taking Network+ certification exam. It is also recommended, but not required, that you have about 12 months of IT networking work experience.
Go to: Set II | Set III
CompTIA Network+ N10-007 - Set I
Congratulations - you have completed CompTIA Network+ N10-007 - Set I.
You scored %%SCORE%% out of %%TOTAL%%. With incorrect multiple attempts, your score is %%PERCENTAGE%%. Your performance has been rated as %%RATING%%
Question 1 |
A | Jumbo frame |
B | Double NAT |
C | Bridge mode |
D | DOCSIS |
E | ADSL |
Question 2 |
A | Data link |
B | Network |
C | Transport |
D | Session |
E | Application |
F | Physical |
G | Presentation |
Question 3 |
A | 3 unit |
B | 2 unit |
C | 1 unit |
D | 4 unit |
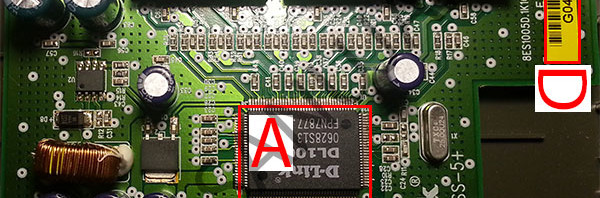
Question 4 |
A | Data Link |
B | Network |
C | Transport |
D | Session |
E | Application |
Question 5 |
A | PPTP |
B | L2TP |
C | FTPS |
D | IPsec |
Question 6 |
A | Fiber-optic cabling |
B | Coaxial cabling |
C | Twisted pair cabling |
D | Enterrpise APs |
Question 7 |
A | Power distribution unit |
B | Powerline extender |
C | Power-over-Ethernet switch |
D | Ethernet-over-power adapter |
E | Ethernet power controller |
Question 8 |
A | Ping |
B | Netstat |
C | Nslookup |
D | Route |
E | Tracert |
Question 9 |
A | Transport |
B | Physical |
C | Network |
D | Session |
E | Presentation |
F | Application |
G | Data link |
Question 10 |
A | Network wiring is run perpendicular to electrical conduit |
B | Light sensors are interfering with the network |
C | Temperature changes are causing attenuation in copper cabling |
D | EMI from the lights is interfering with the network cables |
Question 11 |
A | Setup |
B | Application |
C | System |
D | Security |
Question 12 |
A | 255 255 255.0 |
B | 192.168.0.55 |
C | 255 255 255.0 |
D | 192.168.1.0 |
E | 192.168.1.1 |
Question 13 |
A | Logical network diagram |
B | Asset management files |
C | Wiring schematic |
D | Physical network diagram |
E | MSConfig file |
Question 14 |
A | 192.168.0.0 to 192.168.0.255 |
B | 10.0.0.0 to 10.0.255.255 |
C | 224.0.0.0 to 224.0.255.255 |
D | 169.254.0.0 to 169.254.255.255 |
Question 15 |
A | Point-to-point |
B | Ring |
C | Bus |
D | Peer-peer |
E | Mesh |
F | Point-to-multipoint |
Question 16 |
A | LC |
B | MTRJ |
C | F-type |
D | RJ45 |
E | RJ11 |
F | ST |
Question 17 |
A | Private |
B | IaaS |
C | PaaS |
D | SaaS |
E | Public |
F | Hybrid |
Question 18 |
A | RJ11 |
B | ST |
C | F-type |
D | RJ45 |
E | MTRJ |
Question 19 |
A | Hire a third-party contractor to go on-site |
B | Walk a user through troubleshooting the connection |
C | Use a modem to console into the router |
D | Travel to the branch office |
Question 20 |
A | Brute-force |
B | Port sweeping |
C | Bluejacking |
D | Port scanning |
E | War driving |
Question 21 |
A | The channel has changed |
B | There is a security type mismatch. |
C | There is insufficient antenna power |
D | There is a frequency mismatch |
E | The password needs to be re-entered |
Question 22 |
A | Hex |
B | Binary |
C | Octal |
D | CIDR |
Question 23 |
A | Configure port aggregation |
B | Use port mirroring |
C | Use SQL injectors |
D | Periodically view the server logs |
E | Install an inline tap |
Question 24 |
A | The public key |
B | The private key |
C | The session key |
D | The secure key |
E | The ticket granting key |
Question 25 |
A | Transport |
B | Application |
C | Presentation |
D | Data link |
E | Physical |
F | Session |
G | Network |
Question 26 |
A | It is impossible to have a collision domain in a wireless network infrastructure. |
B | Collision domains occur in layer 1 while broadcast domains occur in layer 2. |
C | It is impossible to have a collision domain in a wired (LAN) network infrastructure. |
D | Both broadcast and collision domains occur at layer 2. |
E | Broadcast domains occur in layer 1 while collision domains occur in layer 2. |
Question 27 |
A | POP |
B | SMTP |
C | LDAP |
D | IMAP |
Question 28 |
A | Control the attenuation of the non-voice traffic across the network links |
B | Control the latency of traffic across the network links |
C | Control the jitter of the affected traffic across the network links |
D | Control the EMI of the multimedia traffic across the network links |
Question 29 |
A | Physical inspection of each site/workstation. |
B | Configure advance intrusion detection and firewall rules on the main datacenter. |
C | Install and maintain advanced enterprise firewall applications. |
D | Perform frequent security and vulnerability updates. |
E | Perform frequent IT audits. |
Question 30 |
A | FTP |
B | HTTP |
C | SMTP |
D | SSL |
E | HTML |
Question 31 |
A | 192.168.0.55 |
B | 10.1.1.255 |
C | 192.168.1.109 |
D | 10.1.0.255 |
E | 192.168.0.1 |
Question 32 |
A | ARP |
B | SCP |
C | FTP |
D | SIP |
Question 33 |
A | A |
B | MX |
C | PTR |
D | MD |
E | CNAME |
Question 34 |
A | Corrupted config files or operating system |
B | Damaged or malfunctioning LAN port |
C | Damaged or malfunctioning fiber port |
D | Double NAT issue |
E | VLAN mismatch |
Question 35 |
A | http://sanuja.com/123456 |
B | http://sanuja.com:123456 |
C | None of the answers are correct because you cannot assign random port numbers. |
D | https://sanuja.com/123456 |
E | https://sanuja.com:123456 |
Question 36 |
A | 161 , 162 |
B | 80 , 443 |
C | 143 , 993 |
D | 5060 , 5061 |
E | 5060 , 3389 |
Question 37 |
A | arp -d |
B | arp -a |
C | arp -s |
D | arp -c |
E | arp -t |
Question 38 |
A | Social engineering |
B | Asset tracking |
C | Geofencing |
D | Tamper detection |
E | Biometric |
Question 39 |
A | Verify file date |
B | Verify file size |
C | Verify file hash |
D | Verify file version |
E | Verify file type |
Question 40 |
A | Pattern recognition |
B | Single sign-on (SSO) |
C | Tamper detection |
D | Biometrics |
E | Hand geometry |
Question 41 |
A | Netstat |
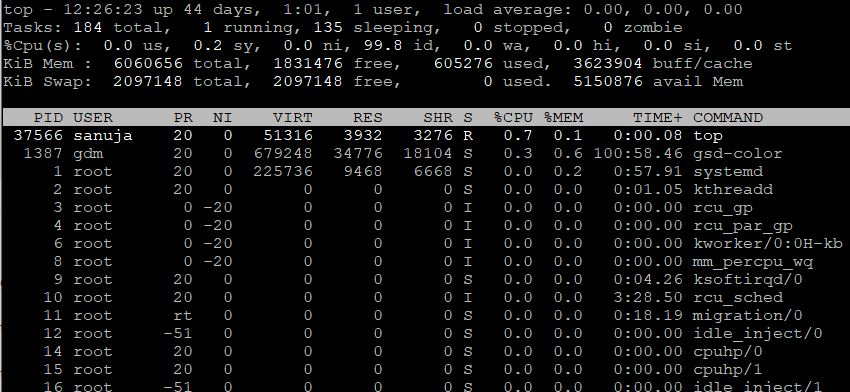
B | Top |
C | Netmon |
D | Syslog |
Question 42 |
A | GBIC |
B | SFP |
C | QSFP |
D | BiDi |
Question 43 |
A | None of the classes |
B | Class B |
C | Class A |
D | Class D |
E | Class C |
Question 44 |
SANUJA.COM 430 IN mx mx1.SANUJA.COM
SANUJA.COM 5 IN mx mx2.SANUJA.COM
SANUJA.COM 430 IN mx mx10.SANUJA.COM
SANUJA.COM 521 IN NS ns1.SANUJA.COM
SANUJA.COM 521 IN NS ns2.SANUJA.COM
SANUJA.COM 521 IN NS ns3.SANUJA.COM
SANUJA.COM 521 IN NS ns4.SANUJA.COM
A | iptables –f SANUJA.COM |
B | NMAP –t SANUJA.COM |
C | dig –t ANY SANUJA.COM |
D | netstat –a SANUJA.COM |
Question 45 |
A | ifconfig |
B | ipconfig |
C | tracert |
D | netstat |
E | ping |
Question 46 |
A | Change management |
B | Standard operating procedure |
C | Process management |
D | Project management |
Question 47 |
A | ICMP |
B | TCP |
C | UDP |
D | IP |
E | Ethernet |
Question 48 |
A | RADIUS |
B | NAC |
C | TKIP-RC4 |
D | LDAP |
Question 49 |
A | DHCP server issue |
B | Spanning tree blocked ports |
C | Duplex/speed mismatch |
D | VLAN mismatch |
E | DNS server issue |
Question 50 |
A | SIP |
B | LLDP |
C | BGP |
D | LACP |
Question 51 |
A | 0 |
B | 2 |
C | 4 |
D | 7 |
E | 6 |
Question 52 |
A | Fault tolerance |
B | Network management |
C | Distributed server system |
D | Remote connection |
E | Site-to-site VPN |
Question 53 |
A | Evil twin |
B | Logic bomb |
C | Social engineering |
D | Wardriving |
Question 54 |
A | traceroute |
B | netstat |
C | ifconfig |
D | ping |
Question 55 |
A | Transport |
B | Network |
C | Physical |
D | Session |
E | Data Link |
F | Presentation |
G | Application |
Question 56 |
A | nmap |
B | netstat |
C | tcpdump |
D | dig |
Question 57 |
A | Biometrics |
B | Tamper detection |
C | Pattern recognition |
D | Geofencing |
E | Face geometry |
Question 58 |
A | DHCP restriction |
B | DHCP option |
C | DHCP relay |
D | DHCP exclusion |
E | DHCP reservation |
Question 59 |
A | Wiring schematic |
B | Circuit diagrams |
C | Asset management files |
D | Logical network diagram |
E | Physical network diagram |
Question 60 |
A | A user application problem |
B | A system-wide problem |
C | A network-wide problem |
D | A wide area newtwork problem |
E | A shared resource problem |
Question 61 |
A | Fibre Channel |
B | iSCSI |
C | CIFS |
D | InfiniBand |
Question 62 |
A | 1023 through 65534 |
B | 49152 through 65535 |
C | 1024 to 49151 |
D | 1 through 1024 |
Question 63 |
A | T-3 |
B | T-1 |
C | E-1 |
D | OC-1 |
Question 64 |
A | A consent to monitoring policy covering company audits of the personal phone |
B | An AUP covering how a personal phone may be used for work matters |
C | An NDA ensuring work data stored on the personal phone remains confidential |
D | Real-time remote monitoring of the phone’s activity and usage |
Question 65 |
A | IGMP |
B | UDP |
C | TCP |
D | ICMP |
Question 66 |
A | Utilize UDP to eliminate packet overhead |
B | Enable jumbo frames on the NAS and server |
C | Encapsulate the storage traffic in a GRE tunnel |
D | Turn off MDIX settings on the NAS and server switchports |
Question 67 |
A | Cut-through |
B | Destination switch |
C | Store-and-forward |
D | Source route |
Question 68 |
A | Wardriving |
B | Social engineering |
C | Logic bomb |
D | Evil twin |
Question 69 |
A | 4 |
B | 3 |
C | 1 |
D | 0 |
E | 2 |
Question 70 |
A | 10GBase-SR |
B | 10GBase-LX4 |
C | 10GBase-LR |
D | 10GBase-CX4 |
E | 10GBase-ER |
Question 71 |
A | LDAP |
B | Local authentication |
C | Single sign-on |
D | TACACS+ |
Question 72 |
A | SLA |
B | IRP |
C | NDA |
D | BYOD |
Question 73 |
A | TKIP |
B | LDAP |
C | 802.1X |
D | Radius |
E | Kerberos |
Question 74 |
A | Have the ISP double the bandwidth |
B | Enable WPA and change the SSID |
C | Configure geofencing |
D | Move from WPA2 to WEP |
Question 75 |
A | Short circuits |
B | Split pairs |
C | Transposed wires |
D | Open circuits |
Question 76 |
A | A gateway |
B | A router |
C | A switch |
D | A hub |
Question 77 |
A | Signal attenuation |
B | Latency |
C | EMI |
D | Crosstalk |
Question 78 |
A | Snapshots |
B | Backups |
C | Failover |
D | Cold sites |
Question 79 |
A | VDSL |
B | HDSL |
C | IDSL |
D | RADSL |
Question 80 |
A | Single-mode fiber optic |
B | Unshielded twisted pair |
C | Shielded twisted pair |
D | Multimode fiber optic |
E | Coaxial |
Question 81 |
A | Security |
B | Application |
C | System |
D | Setup |
Question 82 |
A | UDP |
B | TCP |
C | HTTP |
D | IP |
Question 83 |
A | ping |
B | cpustat |
C | netstat |
D | top |
E | monitor |
Question 84 |
A | A static IP pointing to the passive DB |
B | A private IP pointing to the web front end |
C | A virtual IP pointing to the active DB |
D | A private IP pointing to the web proxy |
Question 85 |
A | vulnerability scanning |
B | social engineering |
C | friendly DoS |
D | session hijacking |
E | penetration testing |
Question 86 |
A | RAID 0 |
B | RAID 1 |
C | RAID 5 |
D | RAID 10 |
Question 87 |
A | iptables |
B | tcpdump |
C | netstat |
D | traceroute |
E | ipconfig |
Question 88 |
A | Captive portal |
B | NAC |
C | WAP |
D | MAC filtering |
E | Port security |
Question 89 |
A | arp -c * |
B | arp -d * |
C | arp -s |
D | arp -a |
Question 90 |
A | Motion detection |
B | Biometrics |
C | Video surveillance |
D | Smartcards |
Question 91 |
A | 19 inches |
B | 16 inches |
C | 24 inches |
D | 12 inches |
Question 92 |
A | Rack diagram |
B | Building blueprints |
C | Logical diagram |
D | Network map |
E | Wiring schematic |
Question 93 |
A | PAP |
B | CHAP |
C | MS-CHAPv2 |
D | EAP |
E | WEP |
Question 94 |
A | Circuit diagrams |
B | Wiring schematic |
C | Physical network diagram |
D | Asset management files |
E | Logical network diagram |
Question 95 |
A | Presentation |
B | Session |
C | Transport |
D | Data Link |
E | Physical |
F | Network |
G | Application |
Question 96 |
A | UPS |
B | SNMP |
C | RAID 1 |
D | Clustering |
Question 97 |
A | WPA2 |
B | PEAP |
C | WPA |
D | WEP |
Question 98 |
A | Set up an SSH session to the desktop. |
B | Perform a DNS lookup on the server. |
C | Configure port security on the switch. |
D | Reference the ARP table in the router. |
Question 99 |
A | RC5 |
B | DB9 |
C | RJ45 |
D | USB 2.0 |
E | USB 3.0 |
Question 100 |
A | Speed |
B | Distance |
C | Bandwidth |
D | Hop count |
E | Ping time |
Question 101 |
A | PaaS |
B | SaaS |
C | IaaS |
D | VPN |
E | Hosted |
Question 102 |
A | netstat |
B | dig |
C | traceroute |
D | route |
E | ifconfig |
Question 103 |
A | Accounting |
B | Administration |
C | Authorization |
D | Authentication |
Question 104 |
A | 802.1x |
B | ACL |
C | NAT |
D | Sticky MAC |
E | NAC |
Question 105 |
A | 16 |
B | 17 |
C | 8 |
D | 15 |
Question 106 |
A | SC to SC |
B | LC to ST |
C | ST to ST |
D | LC to SC |
E | SC to ST |
Question 107 |
A | QoS |
B | SSL |
C | VoIP |
D | CARP |
E | IPv6 |
Question 108 |
A | Hubs |
B | Routers |
C | Bridges |
D | Firewalls |
Question 109 |
A | 80 |
B | 1024 |
C | 995 |
D | 50134 |
E | 1999 |
F | 23 |
Question 110 |
A | VPN concentrator |
B | Proxy server |
C | VoIP gateway |
D | UTM appliance |
Question 111 |
A | Hub |
B | Router |
C | Switch |
D | Bridge |
Question 112 |
A | IMAP |
B | IGMP |
C | IP |
D | ICMP |
Question 113 |
A | Secured |
B | Private |
C | Preshared |
D | Privileged |
E | Public |
Question 114 |
A | Auditing |
B | Authorization |
C | Authentication |
D | Accounting |
Question 115 |
A | Layer 4 |
B | Layer 1 |
C | Layer 2 |
D | Layer 3 |
Question 116 |
A | VLAN hopping is the act of exploiting poor VLAN tagging. Session hijacking is a web-based attack aimed at privilege escalation. |
B | VLAN hopping involves the unauthorized transition from one VLAN to another to gain additional access. Session hijacking involves overriding a user’s web connection to execute commands. |
C | VLAN hopping is a brute force attack executed to gain additional access. Session hijacking involves physically disrupting a network connection. |
D | VLAN hopping involves overriding a user network connection to execute malicious commands. Session hijacking involves compromising a host to elevate privileges. |
Question 117 |
A | Implement spanning tree |
B | Change default admin password |
C | Perform backups |
D | Enable port mirroring |
E | Patch and update |
F | Perform VLAN hopping |
Question 118 |
A | Source route |
B | Transparent |
C | Store and forward |
D | Multiport |
Question 119 |
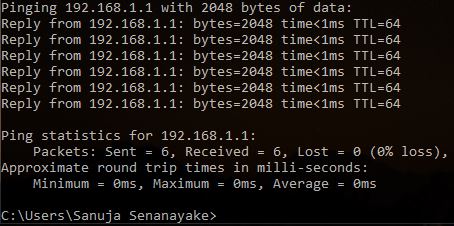
A | ping 192.168.1.1 -l 2048 -n 6 |
B | ping 192.168.1.1 -n 2048 |
C | ping 192.168.1.1 -l 2048 -t 6 |
D | ping 192.168.1.1 -t |
E | ping 192.168.1.1 -l 2048 -t |
Number of messages: -n parameter = 6
Question 120 |
A | Access control lists |
B | Captive portal |
C | Port security |
D | WPA2 |
Question 121 |
A | TXT |
B | A |
C | AAAA |
D | NS |
E | MX |
Question 122 |
A | SYN |
B | END |
C | URG |
D | FIN |
E | PSH |
Question 123 |
A | XSS |
B | Wardriving |
C | Packet sniffing |
D | SQL injection |
E | Directory traversal |
Question 124 |
A | Cross talk |
B | Overcapacity |
C | Wrong passphrase |
D | Channel overlap |
Question 125 |
A | A privilege escalation script |
B | An open mail relay server |
C | A router with default credentials |
D | An SNMPv1 private community |
Question 126 |
A | FCoE |
B | NAS |
C | FTP |
D | iSCSI |
E | SAN |
Question 127 |
A | Ring or circular |
B | Mesh |
C | Bus |
D | Point-to-point |
E | Star |
Question 128 |
A | AAAA |
B | NS |
C | A |
D | TXT |
E | MX |
Question 129 |
A | Permit 192.168.1.143 port 80 |
B | Permit 192.168.1.143 port 587 |
C | Permit 192.168.1.143 port143 |
D | Permit 192.168.1.143 port 110 |
E | Permit 192.168.1.143 port 443 |
F | Permit 192.168.1.143 port 25 |
Question 130 |
A | Application server |
B | KDC |
C | RDP |
D | Client terminal |
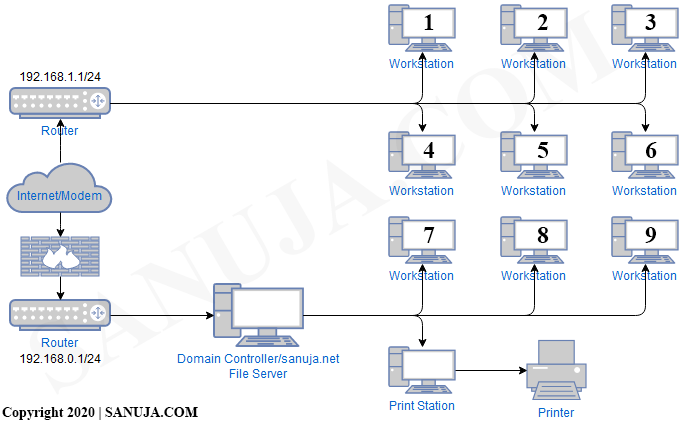
Question 131 |
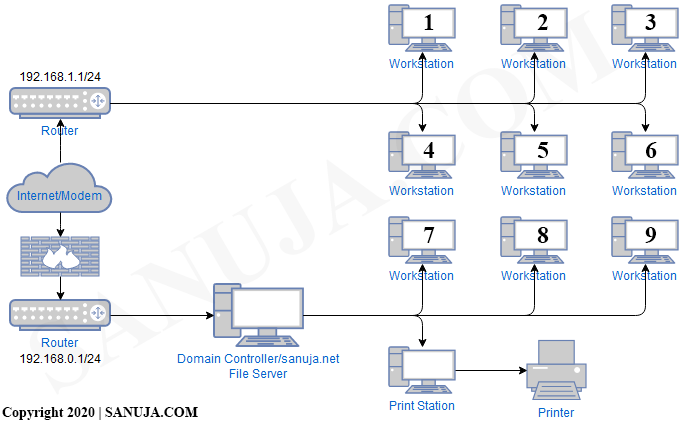
A | Remove the firewall between the Internet/modem and the router. |
B | Add additional printers across both NATs. |
C | Add a firewall between the domain controller and the router. |
D | Remove one of the routers and if requires use VLANs to create separate subnets with specific firewall rules. |
Question 132 |
A | IDF |
B | VRF |
C | TDM |
D | MDF |
Question 133 |
A | Wireless controller |
B | Wireless endpoint |
C | Network firewall |
D | Demarcation point |
E | Demarcation point |
Question 134 |
A | Power redundancy |
B | Power looping |
C | Redundant circuits |
D | Uninterruptible Power Supply (UPS) |
E | Dual power supplies |
Question 135 |
A | Incompatibility with the current network |
B | Inconsistent data accessability |
C | Increased malware exposure |
D | Decreased performance of the internal network |
E | Loss of full control over data resources |
Question 136 |
A | WinMS |
B | Window |
C | MMS |
D | MSS |
Question 137 |
A | ping |
B | pathping |
C | route |
D | netstat |
Question 138 |
A | iptables |
B | nmap |
C | tcpdump |
D | dig |
Question 139 |
A | Network switching |
B | IP address resolution |
C | Name resolution |
D | Password protection |
Question 140 |
A | Install honeypots on the network to detect and analyze potential kiosk attacks before they occur. |
B | Create a new network segment with ACLs, limiting kiosks’ traffic with the internal network. |
C | Install an IDS to monitor all traffic to and from the kiosks. |
D | Enable switchport security on the ports to which the kiosks are connected to prevent network-level attacks. |
E | Create a secondary NAT and connect the kiosks on it hence limit kiosks' ability to access the main network. |
Question 141 |
A | Web proxy |
B | Protocol analyzer |
C | Layer 3 switch |
D | Layer 7 firewall |
E | NAT |
Question 142 |
A | Default gateway |
B | IP address |
C | Subnet mask |
D | MAC address |
Question 143 |
A | Syslog |
B | Performance Monitor |
C | Event Viewer |
D | Network Monitor |
E | ntop |
Question 144 |
A | Somewhere you are |
B | Something you do |
C | Something you have |
D | Something you know |
Question 145 |
A | Gateway |
B | Switch |
C | Router |
D | Bridge |
Question 146 |
A | device hardening |
B | hardware security |
C | tamper detection |
D | biometrics |
E | asset tracking |
Question 147 |
A | SYN, ACK, SYN, ACK |
B | SYN/ACK, SYN/ACK |
C | SYN, SYN/ACK, ACK |
D | SYN, SYN, ACK, ACK |
Question 148 |
A | Authorization |
B | Certification |
C | Encryption |
D | Enrollment |
E | Authentication |
Question 149 |
A | Fibre Channel |
B | iSCSI |
C | InfinitiBand |
D | NAS |
Question 150 |
A | Infrared |
B | Microwave |
C | Fiber optic |
D | Electrical |
Question 151 |
A | RDP |
B | PBX |
C | MTBF |
D | IDF |
E | MDF |
Question 152 |
A | ARP |
B | NAT |
C | STP |
D | PAT |
E | SNAT |
Question 153 |
A | 8P8C |
B | F-type |
C | BNC |
D | MTRJ |
E | RJ45 |
Question 154 |
A | Phishing |
B | Spoofing |
C | DDoS |
D | Ransomware |
E | Session hijacking |
Question 155 |
A | CARP |
B | Quality of service |
C | Round-robin DNS |
D | Voice over IP |
Question 156 |
A | Multiport bridge |
B | Layer 3 repeater |
C | Ethernet hub |
D | Layer 2 router |
Question 157 |
A | Wireless access point |
B | Smartcards |
C | Domain controller |
D | RADIUS server |
E | Biometric systems |
Question 158 |
A | RAID 10 |
B | RAID 0 |
C | RAID 5 |
D | RAID 1 |
Question 159 |
A | Telnet |
B | IPSec |
C | SSL |
D | SSH |
Question 160 |
A | A gateway |
B | A hub |
C | A switch |
D | A router |
Question 161 |
A | Multimeter |
B | Loopback adapter |
C | Tone generator |
D | Cable tester |
Question 162 |
A | RPO |
B | RTO |
C | MIB |
D | BCP |
E | RAID |
Question 163 |
A | Port security |
B | Asset tracking |
C | Physical security |
D | Data security |
Question 164 |
A | VLAN mismatch |
B | Evil twin |
C | Honey pot |
D | Packet intrusion |
E | Rogue DHCP server |
Question 165 |
A | HTTPS server |
B | VPN gateway |
C | Secure server |
D | Authentication server |
E | Encryption key |
Question 166 |
A | Verify the firmware file hash |
B | Apply patches and updates |
C | Change the default credentials |
D | Disable unused switchports |
Question 167 |
A | NAS |
B | IDS |
C | NGFW |
D | RADIUS |
Question 168 |
A | 192.168.0.1 |
B | 175.255.255.255 |
C | 169.254.54.5 |
D | 192.168.1.1 |
E | 175.168.0.255 |
Question 169 |
Image Credit: https://www.tequipment.net/ FlukeNetworks52801009.html
A | By connecting the clips to pins in a punchdown block, you can access telephone circuits in order to test them or place telephone calls. |
B | By touching the end of the tool to a copper cable, you can detect and measure the electrical current flowing through it. |
C | To attach a bulk cable end to an RJ45 connector, you use the tool to squeeze the connector closed, forcing the wire ends to contact the connector’s pins. |
D | When you place the tool at one end of a wire, it generates a tone that can be detected at the other end. |
Question 170 |
A | TGS |
B | Accounting |
C | Auditing |
D | Authentication |
E | Authorization |
Question 171 |
A | -i |
B | -t |
C | -a |
D | -n |
Question 172 |
A | RC4 |
B | 802.1X |
C | TKIP |
D | AES |
E | Kerberos |
Question 173 |
A | 143 |
B | 80 |
C | 110 |
D | 25 |
E | 989 |
Question 174 |
A | BRI |
B | DSL |
C | E1/E3 |
D | PRI |
Question 175 |
A | Update the firmware and drivers on spare network equipment regularly. |
B | Keep purchasing new spare equipment. |
C | Instead of replacing current units during failures, use parts from the spare units to fix the current unit. |
D | Store all spare equipment in a sepearete office building for extra protection. |
E | Do nothing and keep the spare nearby for an emergency. |
Question 176 |
A | VLAN restrictions |
B | Web application firewall |
C | VPN concentrator |
D | Content filter |
E | IPS |
Question 177 |
A | Session hijacking |
B | Blocking |
C | Throttling |
D | Data usage limits |
E | Bandwidth quotas |
Question 178 |
A | 802.1X |
B | WPA2 |
C | WPA |
D | WEP |
Question 179 |
A | Allow the firewall to accept inbound traffic to ports 80,110,143, and 443 |
B | Allow the firewall to accept inbound traffic to ports 25, 67,179, and 3389 |
C | Allow the firewall to accept inbound traffic to ports 21, 53, 69, and 123 |
D | Set the firewall to operate in transparent mode |
Question 180 |
A | Branch-to-server |
B | Host-to-site |
C | Site-to-site |
D | Extranet |
E | Host-to-host |
Question 181 |
A | DSL |
B | ISDN |
C | Cable broadband |
D | Dial-up modem |
Question 182 |
A | 80 |
B | 25 |
C | 110 |
D | 990 |
E | 443 |
Question 183 |
A | SONET |
B | SIP trunk |
C | AAA server |
D | Smart jack |
E | Media converter |
Question 184 |
A | Layer 7 |
B | Layer 2 |
C | Layer 3 |
D | Layer 1 |
E | Layer 5 |
F | Layer 4 |
G | Layer 6 |
Question 185 |
A | PAT |
B | SIP |
C | NAT |
D | VIP |
Question 186 |
A | RG-8 |
B | RJ-45 |
C | RJ-11 |
D | RG-58 |
Question 187 |
A | CCMP-AES |
B | EAP-PEAP |
C | WEP |
D | PSK |
Question 188 |
A | Load balancer |
B | Enterprise firewall |
C | IDS |
D | Wireless controller |
E | Proxy server |
Question 189 |
A | Bus |
B | Ring |
C | Mesh |
D | Star |
E | Ad hoc |
Question 190 |
A | RADIUS |
B | Kerberos |
C | WPA2 |
D | EAP-TLS |
Question 191 |
A | The testing server for the wired network was farther away |
B | The firewall is configured to throttle traffic to specific websites |
C | There is less local congestion on the wireless network |
D | The wireless access points were misconfigured |
Question 192 |
A | Operating system update |
B | BOIS firmware patch |
C | Vulnerability patch |
D | Feature change |
E | Driver update |
Question 193 |
A | NAS |
B | FTP |
C | Fiber channel |
D | Jumbo frames |
E | SAN |
Question 194 |
A | Units |
B | Millimeters |
C | Centimeters |
D | Inches |
E | Number of screw holes |
Question 195 |
A | Fiber distribution panel |
B | 66 block |
C | CMTS |
D | Patch panel |
E | 110 block |
Question 196 |
A | Server clustering |
B | DNS round robin |
C | Muti-ISP connections |
D | NIC teaming |
E | RAID 1 |
Question 197 |
A | QoS |
B | DMZ |
C | DDoS |
D | NAT |
E | RIP |
Question 198 |
A | Airflow and cooling |
B | UPS capability |
C | Power redundancy |
D | Circuit labeling |
Question 199 |
A | SSL client |
B | SSL tunnel |
C | SSL portal |
D | SSL gateway |
Question 200 |
A | High-efficiency mode |
B | Hot backup mode |
C | Combined mode |
D | Redundant mode |
E | Individual mode |
← |
List |
→ |
| 1 | 2 | 3 | 4 | 5 |
| 6 | 7 | 8 | 9 | 10 |
| 11 | 12 | 13 | 14 | 15 |
| 16 | 17 | 18 | 19 | 20 |
| 21 | 22 | 23 | 24 | 25 |
| 26 | 27 | 28 | 29 | 30 |
| 31 | 32 | 33 | 34 | 35 |
| 36 | 37 | 38 | 39 | 40 |
| 41 | 42 | 43 | 44 | 45 |
| 46 | 47 | 48 | 49 | 50 |
| 51 | 52 | 53 | 54 | 55 |
| 56 | 57 | 58 | 59 | 60 |
| 61 | 62 | 63 | 64 | 65 |
| 66 | 67 | 68 | 69 | 70 |
| 71 | 72 | 73 | 74 | 75 |
| 76 | 77 | 78 | 79 | 80 |
| 81 | 82 | 83 | 84 | 85 |
| 86 | 87 | 88 | 89 | 90 |
| 91 | 92 | 93 | 94 | 95 |
| 96 | 97 | 98 | 99 | 100 |
| 101 | 102 | 103 | 104 | 105 |
| 106 | 107 | 108 | 109 | 110 |
| 111 | 112 | 113 | 114 | 115 |
| 116 | 117 | 118 | 119 | 120 |
| 121 | 122 | 123 | 124 | 125 |
| 126 | 127 | 128 | 129 | 130 |
| 131 | 132 | 133 | 134 | 135 |
| 136 | 137 | 138 | 139 | 140 |
| 141 | 142 | 143 | 144 | 145 |
| 146 | 147 | 148 | 149 | 150 |
| 151 | 152 | 153 | 154 | 155 |
| 156 | 157 | 158 | 159 | 160 |
| 161 | 162 | 163 | 164 | 165 |
| 166 | 167 | 168 | 169 | 170 |
| 171 | 172 | 173 | 174 | 175 |
| 176 | 177 | 178 | 179 | 180 |
| 181 | 182 | 183 | 184 | 185 |
| 186 | 187 | 188 | 189 | 190 |
| 191 | 192 | 193 | 194 | 195 |
| 196 | 197 | 198 | 199 | 200 |
| End |
Based on general knowledge and CompTIA guidelines published in 2020.
FAQ | Report an Error
Study outline at: CompTIA Exams Guide
Disclaimer: While every reasonable effort is made to ensure that the information provided is accurate, no guarantees for the currency or accuracy of information are made. It takes several proof readings and rewrites to bring the quiz to an exceptional level. If you find an error, please contact me as soon as possible. Please indicate the question ID-Number or description because server may randomize the questions and answers.